One of the primary criteria for any surveillance, access or security system is the requirement for a consistent and reliable power source, as even the most complex and expensive system solutions will be rendered useless if power is interrupted.
- By JR Andrews
- Apr 01, 2019
In the United States, nearly 20 people per minute are physically abused by an intimate partner, equating to more than 10 million in a single year.
Like many metropolitan cities, Hartford, CT has its share of crimes. And solving those crimes usually involves sifting through an overwhelming amount of data.
- By Kevin Taylor
- Apr 01, 2019

Though traffic and crime are not the only contributing factors that determine a location’s desirability, they are some of the top catalysts that inspire digital transformation within a city.
- By Rich LeCates
- Apr 01, 2019
The confusion I hear in the industry starts with the definitions of these terms: artificial intelligence (AI), machine learning (deep and shallow), and analytics. Some believe these things are all the same and use them interchangeably.
Every interview I get for the magazine is enjoyable, and even entertaining. Every conversation is a story but once in a while I have a lead that I know will stick with me for quite a long time.
- By Ralph C. Jensen
- Apr 01, 2019

See no evil, hear no evil, speak no evil: It is tempting for physical security professionals to take this passive approach to cybersecurity.
- By Tom Galvin
- Apr 01, 2019

The banking market continues to evolve due to the growing use of mobile devices, as more branch operations aim to enhance convenience and service for the customer.
- By Matt Tengwall
- Apr 01, 2019
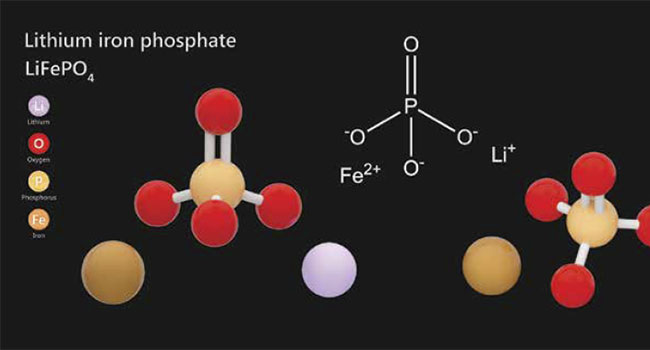
Securing outdoor assets can be a tricky proposition. For starters, traditional outdoor security systems are expensive.
- By Fredrik Wallberg
- Apr 01, 2019
Video surveillance management is becoming increasingly sophisticated in terms of operational capabilities, including the type and scope of analytics available.
- By Peter Ainsworth
- Apr 01, 2019