Ex-president's Home without Alarm System for 13 Months
- By Ginger Hill
- Apr 23, 2015
I’ve always thought that the United States is failing at taking care of our senior population. Our seniors have seen things and done things that we can only dream about. They are a history book just waiting to explode with knowledge, if only we’d give them a chance. It seems that it doesn’t matter if the senior is male or female, rich and/or famous, unknown or even an ex-President; our senior population gets swept to the side.
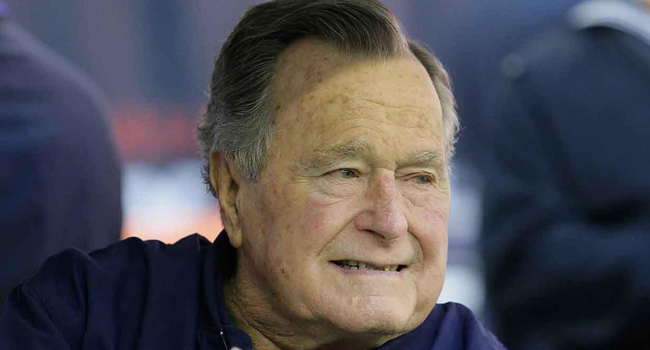
In 2010, an agency expert warned Secret Service officials that the alarm system in former president George H.W. Bush’s home was aging and likely to fail. Not a good situation since it monitored the Bush’s property and home, a high target for terrorists, criminals and people who simply don’t like them. But, according to a report written by the Department of Homeland Security’s inspector general, officials rejected the request to replace the ex-president’s security system.
The Bush’s 20-year-old alarm system stopped operating in September 2013 and it wasn’t until at least 13 months later that they system was replaced. To make up for the system not working, the Secret Service added an agent to rotate positions around the property; however, an additional agent isn’t sufficient to replace an actual alarm system. Humans can miss certain things that an alarm system can pick up.
Chairman of the House Oversight and Government Reform Committee, Republican Representative Jason Chaffetz said, “To no replace a failing system for more than a year is wholly and totally unacceptable.”
I have to agree with Chaffetz. Bush, Sr. is 91-years-old, and at this age, I’m sure as a Texan he’s still good with a shot gun, but not so much with defending himself or his wife Barbara with physical contact. Should something devastating had happened within those 13 months of no alarm system, this would be yet another case of not taking proper care of our senior population.
(Image from abc7.com.)
About the Author
Ginger Hill is Group Social Media Manager.