Several Schools across New Jersey and Massachusetts Receive Threats
- By Sydny Shepard
- Jan 19, 2016
The FBI has joined a police investigation into bomb threats sent to about a dozen schools in Massachusetts and nine more in New Jersey. Many schools in the northern states have been put on lockdown, evacuated or participated in early release of faculty and students.
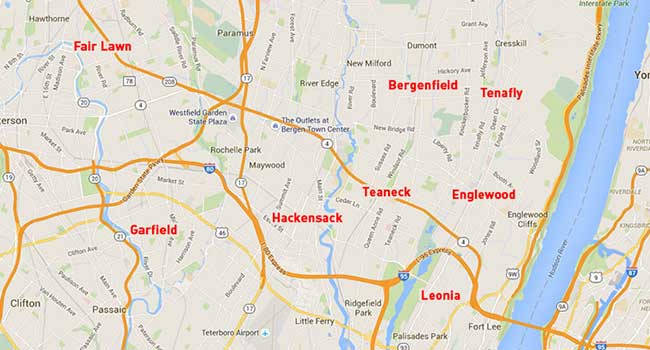
The threats came to high schools in Leonia, Tenafly, Teaneck, Garfield, Fair Lawn, Hackensack, Englewood and Bergenfield, according to Bergen County Sheriff’s spokesman Michael Saudino, as cited by the local media. Clifton High School, in Passaic County, also received a bomb threat via voicemail.
All the schools from several areas spanning across New Jersey and Mass. all received bomb threats around 8:50 a.m., because of the similarities police believe the phoned in threats to be automated.
The latest threats come after a series of threats to at least nine schools on Friday, Jan. 15. While the law enforcement officials scrambled, all of the threats turned out not to be real.
The FBI is now overseeing whoever is responsible for making the calls, while State Police and local police are handling the immediate response, according to David Procopio, a State Police spokesman.
“The [State Police] Bomb Squad and local police departments are handling the individual call outs to the schools as they come in,’’ Procopio said. “As for the overarching investigation into the source or sources of the series of threats, the FBI Boston is taking the lead with State Police from the Commonwealth [Law Enforcement] Fusion Center assisting.’’
While there are no indication that the threats are real, schools and law enforcement officials are taking all steps necessary to procure safety for students and facility of implicated campuses.
This is a developing story. Stay tuned for more information.
About the Author
Sydny Shepard is the Executive Editor of Campus Security & Life Safety.