
Ever, a photo storage and backup app, reportedly trained a commercial facial recognition system using millions of images uploaded to the service without notifying users.
- By Jessica Davis
- May 10, 2019

Microsoft has announced a new platform called ElectionGuard, which aims to increase election security and transparency.
- By Jessica Davis
- May 10, 2019

Technology is providing small and medium-sized businesses (SMBs) of all industries a tremendous opportunity to grow and better manage their business.
- By Manny Johl
- May 09, 2019

One student is dead and eight others were injured after a shooting Tuesday at the STEM School Highlands Ranch in Highlands Ranch, Colo., the Douglas County Sheriff’s Office said. Two suspects are in custody.
- By Jessica Davis
- May 09, 2019

The Al Noor Masjid, one of the mosques targeted in the deadly Christchurch mosque shootings on March 15, is installing security cameras that use artificial intelligence to detect whether someone is armed.
- By Jessica Davis
- May 08, 2019

The tenth version of Android will include finer control over privacy and improvements to Android security updates, Google announced Tuesday at its I/O 2019 event
- By Jessica Davis
- May 08, 2019

With its new All Access program, Tampa International Airport will let non-ticketed people go through security and enter an airport terminal in order to see their loved ones to their terminal or greet them right as they arrive
- By Jessica Davis
- May 07, 2019

People who belong to Generation Z may be overconfident about their online account security, suggests a recent survey commissioned by Google
- By Jessica Davis
- May 07, 2019

Find out how you should respond to being hacked.
- By Jerry Young
- May 06, 2019

New York Governor Andrew Cuomo has directed State Police to increase their presence near houses of worship across the state as Muslims prepare for the holy month of Ramadan.
- By Jessica Davis
- May 03, 2019

In response to passenger outcry about privacy, United, Delta and American Airlines are now covering the small cameras in the back-of-seat units on their planes.
- By Jessica Davis
- May 03, 2019
Mission 500, a 501c3 charitable organization born from the professional security industry to serve children and families in need across the U.S., raised over $145,000 at its tenth annual Security 5K/2K Run/Walk at this year's ISC West show, April 9-12 in Las Vegas, NV.

The U.K. government is looking to step up IoT security against cybercriminals.
- By Sydny Shepard
- May 02, 2019

The suspected shooter was taken into custody within minutes of the shooting.
- By Sydny Shepard
- May 02, 2019

ER doctors say they are dealing with more patient assaults and would recommend more security measures to increase employee safety.
- By Sydny Shepard
- May 01, 2019

Today, many video surveillance systems use IP-based equipment, which sends recorded video across ethernet cabling to local, remote, and cloud-based recorders, often using the same LAN infrastructure that is used by general office workers.

The inspector general believes D.C.'s transportation system is at a higher risk of cybersecurity attacks.
- By Sydny Shepard
- Apr 30, 2019

Security has been heightened at synagogues in Sacramento following the shooting at a San Diego synagogue Saturday, which left one dead and three injured.
- By Jessica Davis
- Apr 30, 2019

One person died and three others were injured in an shooting on a synagogue in Poway, Calif.
- By Sydny Shepard
- Apr 29, 2019

The readers will record license plate information of vehicles inside BART parking lots when they enter and leave
- By Sydny Shepard
- Apr 29, 2019

There are a number of common misconceptions about endpoint security.
- By Jerry Young
- Apr 29, 2019

Six reasons companies should implement a Zero Trust Security Mode.
- By Michael Sciacero
- Apr 26, 2019

Some common areas and issues to keep growing your business, not your security risk.
- By Gary Brown
- Apr 26, 2019
The second annual summit hosted by ISC Security Events, PSA Security Network and the Security Industry Association will tackle a variety of the latest cyber-physical security trends.

A driver intentionally plowed into pedestrians in California and injured eight people, according to police.
- By Sydny Shepard
- Apr 25, 2019

Four sets of steel bollards have been installed on Memphis' iconic Beale Street as part of a safety improvement plan.
- By Sydny Shepard
- Apr 25, 2019

When it comes to citizen safety, the police cameras in Indianapolis are meant to keep an eye on crime and help catch potential threats.
- By Sydny Shepard
- Apr 25, 2019
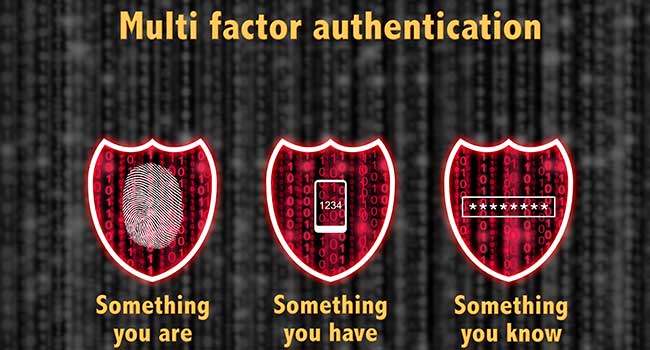
The U.S. Army is working toward adding more authentication measures to provide more options to access Army online resources while maintaining information technology system security.
- By Jessica Davis
- Apr 24, 2019

Beyond user privacy, we’ve seen GDPR impact companies in other ways.