
Security is now being analyzed during the development process to account for every variable.
- By Jeff Keyes
- May 20, 2019

Here's what you need to know about WhatsApp's major security flaw.
- By Sydny Shepard
- May 16, 2019

A bug in the iOS Twitter app impacted the privacy of its users.
- By Sydny Shepard
- May 15, 2019

Binance is making significant security changes after 7,000 Bitcoins were stolen.
- By Sydny Shepard
- May 13, 2019

Microsoft has announced a new platform called ElectionGuard, which aims to increase election security and transparency.
- By Jessica Davis
- May 10, 2019

Technology is providing small and medium-sized businesses (SMBs) of all industries a tremendous opportunity to grow and better manage their business.
- By Manny Johl
- May 09, 2019

People who belong to Generation Z may be overconfident about their online account security, suggests a recent survey commissioned by Google
- By Jessica Davis
- May 07, 2019

Find out how you should respond to being hacked.
- By Jerry Young
- May 06, 2019

The U.K. government is looking to step up IoT security against cybercriminals.
- By Sydny Shepard
- May 02, 2019

The inspector general believes D.C.'s transportation system is at a higher risk of cybersecurity attacks.
- By Sydny Shepard
- Apr 30, 2019

Some common areas and issues to keep growing your business, not your security risk.
- By Gary Brown
- Apr 26, 2019
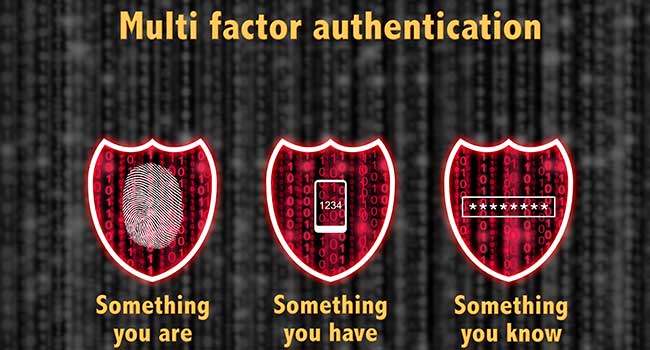
The U.S. Army is working toward adding more authentication measures to provide more options to access Army online resources while maintaining information technology system security.
- By Jessica Davis
- Apr 24, 2019

Hospitals are often in the news due to data breaches, and email hacks are often the cause.
- By Kayla Matthews
- Apr 19, 2019

Many companies are employing System and Organization Controls reports before procuring vendors' services.
- By Brad Thies
- Apr 18, 2019

What went wrong?
- By Kayla Matthews
- Apr 18, 2019

Six things you can do to be proactive against potential cyber crimes.
- By Kayla Matthews
- Apr 17, 2019

Are voice-enabled devices making you more vulnerable to cyberattack?
- By Sydny Shepard
- Apr 16, 2019

No one really knows why airlines have become a target as of late but with the rate of attacks this high, something is definitely going on.
- By Matthew Walker-Jones
- Apr 08, 2019

Facebook is in trouble again.

Strong passwords, two-factor authentication and good cyber hygiene will keep your personal information protected while browsing popular social media accounts.
- By Susan Alexandra
- Apr 04, 2019