Partnership enables organizations to easily scan code and eliminate software risk.

Security market to see rise of opportunities in cloud data center security.
- By Ginger Hill
- Aug 12, 2015

Since 2010 high-ranking officials' vacation plans, emails to friends and other correspondence has been targeted by China.
- By Ginger Hill
- Aug 11, 2015
New partnership helps ensure data integrity and operational continuity if a cyber-incident occurs.
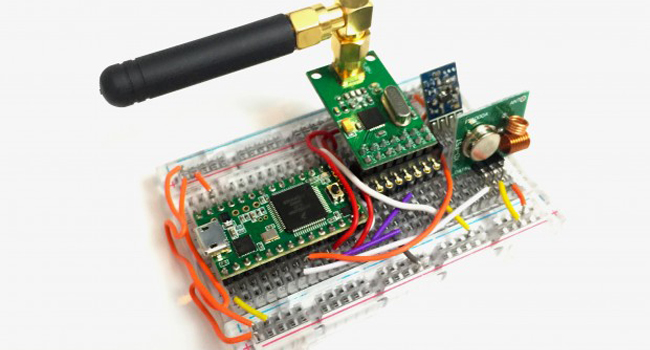
Small $30 device - Rolljam - enables entry into two of your most private places.
- By Ginger Hill
- Aug 10, 2015
Enables monitoring centers to leverage cloud services, including Video Verification, 24/7 Live Intervention, Virtual Guard, Virtual Escort, and Virtual Assistant.
To deliver agentless endpoint security to French market.
Provides common video interface for a wide range of vertical market applications.
Recent hacks expose personal information about millions of people.
- By Alison May
- Aug 06, 2015

Windows 10 features a number of security updates and settings that are important to know, even if you didn’t read the fine print.
- By Matt Holden
- Aug 05, 2015

Some public Wi-Fi hotspots are provided by con artists.
- By Matt Holden
- Aug 04, 2015

Intersecting business into the professionalization of information security debate.
- By Martin Zinaich
- Aug 04, 2015

The funding was led by TPG Growth.
- By Matt Holden
- Aug 03, 2015

5 steps to help professionalize the cybersecurity workforce.
- By Martin Zinaich
- Aug 03, 2015

Five key areas of understanding for information security directors.
- By Martin Zinaich
- Jul 31, 2015

Breaches of all sizes - small, medium and large - ruin reputations and can cost millions of dollars.
- By Martin Zinaich
- Jul 30, 2015

Bolting on security after the fact is always more costly, time consuming and less effective.
- By Martin Zinaich
- Jul 29, 2015

The devices can be hacked using a simple MMS message.
- By Matt Holden
- Jul 28, 2015

International Information Systems Security Certification Consortium of 1988 formed among several professional organizations to create a global information security certification process for professionals and address the need for standardized curriculum.
- By Martin Zinaich
- Jul 20, 2015

What does information security have in common with Eastern Air Lines Flight 401? It’s an odd question, with an important — and potentially tragic — answer.
- By Martin Zinaich
- Jul 15, 2015