
ISC West 2023 is right around the corner! This year’s trade show is scheduled from March 28–31 at the Venetian Expo in Las Vegas, Nevada. The Campus Security & Life Safety and Security Today staff will be on hand to provide live updates about the security industry’s latest innovations, trends, and products.
- By Matt Jones
- Mar 21, 2023
Award-winning global security leader, Gallagher, is excited to announce that Melissa Vidakovic has been named marketing director for the Americas. Melissa joins Gallagher with nearly 20 years of marketing experience in technology and software for companies across North America.
We all continue to see common themes across the headlines: Economic downturn, cross-industry job cuts and global geopolitical uncertainty. For businesses around the world, the turbulent situation can create unintended gaps in critical systems or processes that are core to operations.
- By Luke Tenery, Nathan Fisher
- Mar 20, 2023

A short three years ago we were all pondering whether to attend any tradeshows all thanks to COVID-19. Sorry to bring that nightmare up again, but it seems that little pandemic is in the rear-view mirror, and it’s time to meet again.
- By Ralph C. Jensen
- Mar 20, 2023
St. Louis-based Will Electronics is pleased to welcome, Ted Serve to its team as an account manager. He brings two decades of strong sales experience in the commercial security industry.

The International Security Conference (ISC), in collaboration with premier sponsor Security Industry Association (SIA), announced five of this year’s ISC West Keynote Series speakers. ISC West will kick off its annual conference on March 28 (SIA Education@ISC: March 28-30 | Exhibit Hall: March 29-31) at the Venetian Expo in Las Vegas, Nevada.
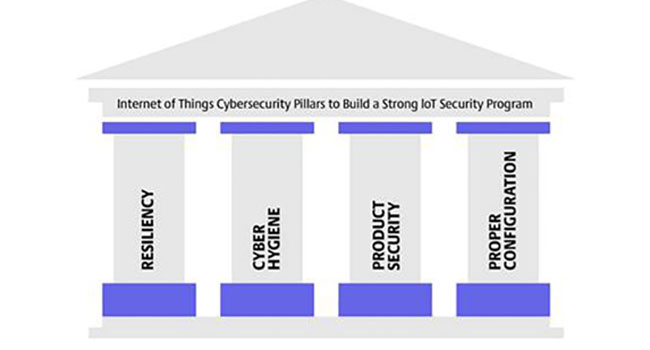
For our second pillar about the Industrial Internet of Things (IIoT) Pillars of Security, we are going to discuss what cyber hygiene looks like for IoT devices.
- By Will Knehr
- Mar 17, 2023

In recent years, the term “digital transformation” has been one of the most frequently used buzzwords across industries. On its most basic level, it refers to the reimagining of how an organization leverages its technology systems to improve business processes.
- By Matt Tengwall
- Mar 16, 2023
Securitas Technology has officially launched, bringing together two of the leaders in electronic security: Securitas Electronic Security and STANLEY Security.
Electronic Security Factory Rep Firm LRG, inc has announced that effective March 13 that company veterans John Swinford and Kenny Hilton have purchased the organization from Chris Lanier.
Energy security tops the list of the ‘most exciting’ areas of smart utility development, ahead of climate-related and disaster management technologies.
Optiv, the cyber advisory and solutions leader, today announced it has acquired Maryland-based ClearShark LLC and ClearShark Services Inc. (collectively ClearShark), a premier advisor and top value-added reseller of cybersecurity and modernization technology to the federal government.

Across the United States, manufacturing facilities, distribution centers, truck yards, parking lots and car dealerships all have a common concern. They are targets for catalytic converters. In nearly every region, cases of catalytic converter thefts have skyrocketed.
- By Patrick Kelly
- Mar 13, 2023
Allied Universal® has announced the acquisition of Landmark Event Staffing Services, a comprehensive event security and guest services company supporting a wide range of venue and event clients nationally.

A wayward driver. A medical emergency. Maybe someone who wants to inflict harm. These are all examples of a vehicle jumping on a sidewalk and causing injuries to pedestrians and workers. It is impossible to foresee every potential scenario where this might happen but the one solution that can stop the vehicle from doing damage are crash-rated bollards, with an emphasis on “crash rated.”
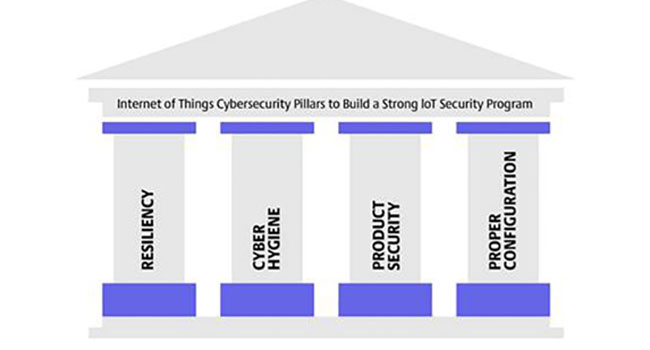
The world has seen a significant increase in cyber-attacks aimed at critical infrastructure and security products in the last few years, with Industrial Internet of Things (IIoT) devices such as security cameras, becoming prime targets for hackers.
- By Will Knehr
- Mar 10, 2023

Necessity may be the mother of invention, but Rently is the mother of inventing self-guided touring for rental properties.
- By Erik Glassen
- Mar 10, 2023

The U.S. Environmental Protection Agency (EPA) recently released a memorandum stressing the need for states to assess cybersecurity risk at drinking water systems to protect our public drinking water.