
Traditionally, electrical substation security was aimed only at preventing access to stop vandalism and improve safety. Today, however, security efforts have been redefined to address new threats in order to protect critical infrastructure.
- By Reinier Tuinzing
- Dec 01, 2015

When I’m asked what role access control devices and technologies play in a structure’s overall sustainability, my thoughts usually wander first to LED lighting.
- By Aaron Smith
- Dec 01, 2015

In the weeks following the massive explosion at a warehouse owned by Ruihai International Logistics in the Chinese port of Tianjin, investigators are getting a better idea of what led to the disaster that killed 173 people—104 of whom were firefighters—and injured hundreds more.
- By Glenn Trout
- Dec 01, 2015

Providing security for a house of worship wasn’t on my radar until recently. Dylann Roof changed all that when he opened fire on the Emanuel African Methodist Episcopal Church in downtown Charleston, S.C.
- By Ralph C. Jensen
- Dec 01, 2015
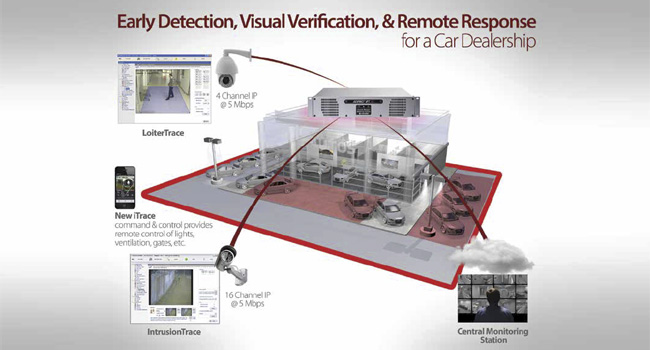
Car dealerships present a complex security challenge because they stock high-end models for the public to see, placing high-value assets out in the open where theft and damage can occur.
- By Katie Merluzzi
- Dec 01, 2015

For the highest level of security possible, Paramount chose to invest in enterprise command center software (ECCS) by SureView Systems to consolidate all of its security and life safety systems across the globe in a simple, effective and centrally manageable security management solution.
Total Recall is the video surveillance integrator for the Statue of Liberty

France ensures the safety of world leaders arriving in Paris for the COP21.
- By Sydny Shepard
- Nov 30, 2015
A shooting at a Colorado Springs Planned Parenthood leaves three dead and nine wounded.
- By Sydny Shepard
- Nov 30, 2015
FLIR Systems, Inc. announced today that it has acquired DVTEL, Inc., a provider of software and hardware technologies for advanced video surveillance, for approximately $92 million in cash.