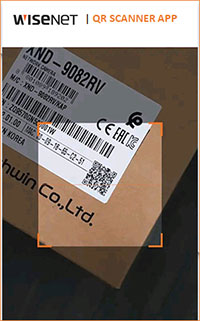
Wisenet QR Scanner App
New app helps reduce installation time and minimize costs
Hanwha Techwin America has announced a new app for systems integrators. The new Wisenet QR Scanner App is designed to help quickly create a list of all Wisenet devices associated with a specific project, without having to take the products out of their packaging. The QR code is found on the outside of the product carton, the bottom of the device, as well as on an included extra sticker for Wisenet modular cameras. This allows a technician to place the sticker on drawings to fully capture the device information.
The app, which can be downloaded from the Apple App Store and Google Play can run on any smart mobile device. It is able to capture information on all the latest generations of Wisenet products, including model names, serial numbers, and MAC addresses. This information can then be used to create a Bill of Materials (BOM) to verify that an order has been fulfilled, and ensure that all devices have been installed. IT managers can use it to keep track of devices on the network and their MAC addresses.
In addition, the app supports offline device registration with the Wisenet Device Manager software tool. A file is exported from the app and edited on a PC to enable installation engineers to configure the products including pre-programming the IP address, setting an initial password, and more. When the configuration is edited offsite, the imported file will then pre-program the configuration when on-site, saving time and allowing better allocation of onsite and offsite staff.
“While installing a small number of cameras will likely have little impact on cost, the labor involved in tracking model names, serial numbers, and associated parts for hundreds of cameras can be significant. That’s why at Hanwha, we put so much effort in not only designing cameras that are easy to install but also in creating tools like the new QR scanning app to allow our systems integrators to focus on what they do best: advising customers, planning projects and ensuring a smooth installation instead of spending hours on tracking model names and serial numbers,” said Ray Cooke, vice president - Products, Solutions and Integration, Hanwha Techwin America.