Selecting the Right Access Control System
You have the necessary experience, but think about the specifications for the job
- By J. Matthew Ladd
- Mar 01, 2019
With a password on each computer and a cardbased
access control system on the door, many
businesses feel they have their bases covered
when it comes to both logical and physical security.
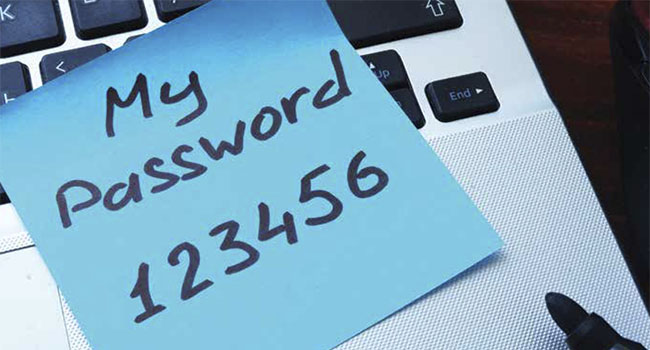
The password for the logical access control system, which provides
authorization into a computer system, they will argue, prevents
just anyone from logging onto a computer—unless the computer’s
owner has a sticky note with their password attached to the screen
or they have shared their password with a friend. Then the laptop or
desktop is easily accessible by others.
No Trespassing
The card will keep strangers out of the building. This works unless
the credential is lost or stolen or passed along by a well-meaning employee
to a co-worker who forgot his card. Access works on the premise
that the user presents one of two items: something they have, like
a card; or something they know, such as a password.
Whether you are running a small business office, doctor’s office,
coffee shop or retail store, it is important to ensure that you protect
staff and assets. While for some this may mean simply locking the
front door at night with a key, the introduction of new technology
at lower price points now means that every business can afford the cost of access control today.
However, accompanying these lower priced options also means
there are a lot of access control systems on the market to choose, such
as standalone systems for one to four doors, mid-size systems that
use single-factor authentication such as a keypad or proximity card,
or large-scale systems that enable corporations to provide access to
employees at multiple facilities in different states while using a single
credential. How do you choose what is best for you?
If cost is your concern, consider a card based or keypad system.
With a card-based system, the small business can use a proximity
card and reader system that allows them to issue an access control
card to employees. This can be an ideal approach for a business with
multiple locations where they want someone to have access to more
than one location. Using a proximity card to access the building also
cuts down on re-key costs when an employee leaves.
Another cost-effective option is to install a keypad system on the
exterior of an office door. When an office manager enters his pin
number, it can unlock the door for the day and also provide a report
on the open and close times of that location. This information can be
accessed remotely by the retail manager to lock and unlock the door.
A Unique Pin
In addition, the administrator of the system can issue multiple pin
numbers to employees, so that each person has a unique pin. That
pin number can be easily deactivated if the employee no longer works
at that location. Still, while these options are most cost effective and
may work perfectly for some businesses, others required some added
security measures.
An option to combat this is multiple-factor authentication, which
requires credentials that address both the logical and physical dynamics
of a security system, in turn taking your system to the next level.
Up until recently, this higher level of security was limited to certain
upper echelon users such as corporate executives, IT administrators
or others whose information and access was considered more important.
For example, a CEO may have to both present a card and punch
in an access code or use his or her fingerprint to open the door to the
executive suite. The desktop used by the head of IT is protected by
both a password and a swipe of his or her access card on an auxiliary
reader attached to the computer.
Cost and complexity of instituting this technology have been cited
in the past as reasons to restrict the use of additional safeguards to a
small percentage of the corporate population, but increasingly those
arguments are going by the wayside.
Security systems integrators are already installing card-based access
control systems at a steady pace, so why not work with that existing
credential and add a layer of logical access on top of it?
The mobility of the standard user, who takes his laptop home on
the weekends or travels for business, makes having at least two-factor
authentication for added logical security more significant. The same
is true with protecting certain physical assets or areas such as a hospital’s
drug supply closet or the records room at a financial institution.
Installing systems requiring multi-factor authentication can prevent
costly or even regulatory mistakes in these key areas.
With the different types of access control systems in mind, there
are still a few questions to ask before deciding on a perfect fit.
The first thing you should ask is whether the system is easy to
use and to manage. Next to price, ease of use is typically the most
important factor to take into consideration when looking to implement
an access control system. Who is going to manage the system
on the back end and add a new cardholder or revoke privileges
when someone leaves the company? Do you need a system that offers
a web-based interface so that you can remotely manage this
task on your own, or do you plan to hire your systems integrator
to oversee that service?
Answering the Question
Before you implement any access control system, it’s important to
answer this question, otherwise the system can become compromised
quickly if access rights are not updated on a regular basis.
Next, users should take a look at the kind of functionalities their
facility needs. It’s important to select an access control system that
aligns with your business needs. Do you have a lot of employees that
require access to an office or facility during the weekend or evening
hours? Or do you need to keep a few key rooms, such as an IT server
room or supply closet, under lock and key and only accessible to a
few select employees?
Also, will you need to monitor who comes and goes into the facility
and need to create a detailed report on access times and who entered
the facility? In some instances, a keypad can provide adequate
security for a small business or to limit access to a specific area within
a secure building. However, a keypad is not an ideal solution for high
security areas because pins can be easily shared with other people.
Instead, it is better to use a keypad and card reader combination to
ensure multi-factor authentication.
Users should keep in mind that many entry-level access control
systems do not offer third party integration. This means that if you
plan to integrate video, elevator controls or an HR system in the future,
it’s important to look beyond an entry-level system to future
proof your system.
While you might not need these exact integrations today, be sure
to look out five years or longer as to what your access control needs
may look like. If you expect to add more employees, then an access
control system with future capabilities may be the best option. An access
control system that can integrate with Active Directory or PeopleSoft,
for example, will enable you to integrate security functionality
with human resources, so that when you onboard a new employee
it becomes a single process to get them access to the building when
they are entered into the HR system as a new employee. The same is
true if that employee leaves the company—HR can deactivate their
access privileges while changing the employee’s employment status.
Lastly, set a budget and stick to it. Price is always a challenging
component because projects often are driven by a set budget, but
many businesses also require a quality system that is reliable. Because
the access control market offers numerous solutions, from standalone
systems to IP-based systems, customers have numerous options from
which to choose at a variety of price points.
A keypad-based system may be more economical for businesses
with only a few access points to secure. These types of systems eliminate
the added expense associated with purchasing and replacing
proximity cards, for example. However, a business that has multiple
access points to secure, requires detailed after-hours building access
reporting or has a large number of employees may need to deploy a
software-based system, which is generally more expensive.
Working in partnership, integrators, physical security personnel
and the IT department can leverage the investment in the physical access
control system into one that brings a higher level of security by
tapping into the logical side as well. No matter the
size of your business or your budget, the security
market offers many different access control systems
from which end users can choose. The challenge
is, of course, deciding which one.
This article originally appeared in the March 2019 issue of Security Today.