
Facebook users have found that a phone number they added to their account for the sole purpose of two-factor authentication can be used to look up their account by advertisers and strangers.
- By Sydny Shepard
- Mar 06, 2019

Phillies security director Sal DeAngelis said that two years ago, the team took notice of the way terrorists were using vehicles in their attacks. They realized that they needed to update the park’s security in response.
- By Jessica Davis
- Mar 05, 2019

“We found that you could break out of the kiosk and interact with the underlying Windows operating systems, and from there do things like drop malware or open up the database,” said Daniel Crowder, research director at the IBM X-Force Red security unit.
- By Jessica Davis
- Mar 05, 2019

What can you do to protect your personal data in 2019?
- By John Heath
- Mar 05, 2019

Bossier, La. maximum-security prison to undergo sweeping security upgrades
- By Sydny Shepard
- Mar 04, 2019

TikTok, a popular video-sharing app, has agreed to pay $5.7 million to settle allegations that it collected data on children.
- By Sydny Shepard
- Mar 04, 2019

The solution isn’t to be afraid of mobile in healthcare
As technology has advanced, security has branched out beyond simple surveillance and intruder deterrence.
Artificial intelligence continues to redefine the capabilities of physical security systems and shape customer demands.
- By Fredrik Wallberg
- Mar 01, 2019
With a password on each computer and a cardbased access control system on the door, many businesses feel they have their bases covered when it comes to both logical and physical security.
- By J. Matthew Ladd
- Mar 01, 2019

The following predictions for ISC West 2019 dive deeper into how these innovations, among others, will help move the security industry forward.
- By Joe Oliveri
- Mar 01, 2019

Back when IT was dominated by on-premises data centers, storage options were fairly straightforward and securing storage resources was relatively simple compared with today’s far more complex storage landscape.
- By Richard Diver
- Mar 01, 2019

Hospitals and other healthcare facilities face unique security and surveillance challenges.
- By Courtney Dillon Pedersen
- Mar 01, 2019

Companies large and small are now actively seeking a fresh approach to optimizing their physical and logical security operations and managing their risk, while capping or reducing their total cost of ownership (TCO).

As key stakeholders look to implement AI into their workflow, many find that security and safety is a commonsense place to begin.
- By Brent Boekestein
- Mar 01, 2019

For the County of Travis in Austin, Texas, research, dedication and the right team resulted in the perfect integrated security solution for its sprawling campus and multi-location facilities.
- By Michael Bone
- Mar 01, 2019

Governments are implementing innovative programs that are revolutionizing how the world looks at identity and citizenship.
- By Steve Warne
- Mar 01, 2019
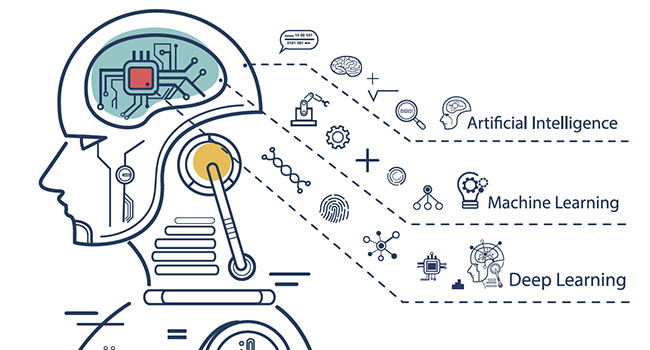
The past few years have seen significant advancements in computing power. With this, machines seem to have a greater ability to learn about us and participate in our lives.
- By Sean Lawlor
- Mar 01, 2019

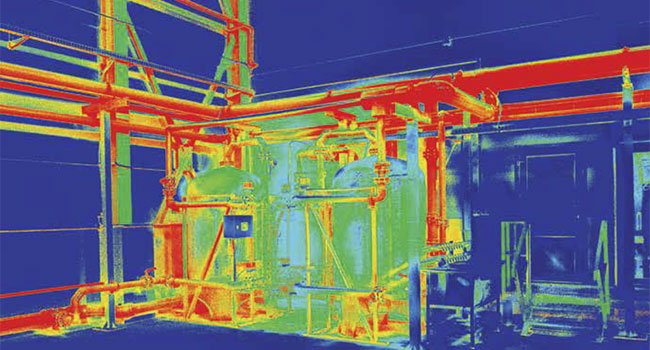
Natural resources being extracted at a mining or quarry operation not only have monetary value, but may also be critical components of medical, military, and industrial processes.
- By Dana Pruiett
- Mar 01, 2019

The attack on a Jewish institution comes amidst unprecedented year-over-year increases in anti-Semitic incidents and hate crimes directed against the Jewish community in North America.
- By Michael Masters
- Mar 01, 2019
Security at the southern border is critical, but let’s not talk about illegal immigration. There is an issue more compelling and serious than what you’ve been seeing in the headlines recently.
- By Ralph C. Jensen
- Mar 01, 2019

When dealing with airport and border security, we need databases, we need to share information and we need law enforcement.
- By Martin Zizi
- Mar 01, 2019

Millions of video surveillance cameras around the world are losing money.
- By Scott Seraboff
- Mar 01, 2019

Like many gaming venues, the lighting scheme at the Hard Rock Hotel & Casino Tulsa in Oklahoma focuses on creating an atmosphere of fun and excitement.
- By Steve Darragh
- Mar 01, 2019

The first step in any security plan is assessing the risk that could impact a company, venue and/or business sector.
- By Tim Williams
- Mar 01, 2019
People are always trying to predict industry trends, but virtually all of the predicted trends I have read lately are just a subset of the benefits offered by cloud managed video.
- By Richard Sheppard
- Mar 01, 2019
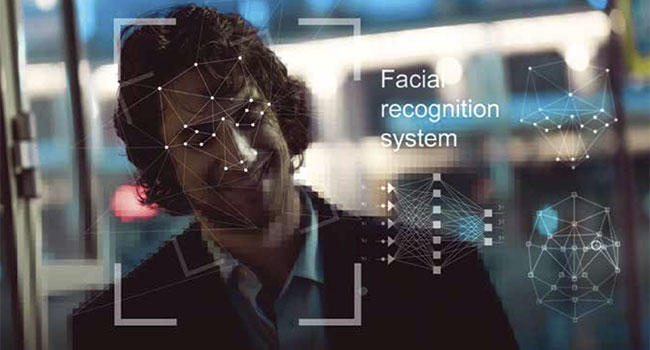
From simple photo IDs of the past to 2D barcodes and the now ubiquitous use of video cameras, businesses, schools and venues are constantly looking for better ways to protect people and property.
- By Denis Petrov
- Mar 01, 2019

"We have identified Miami as an innovation airport, which means as we bring in new technology on and we want to test it in the live environment, we bring it down to Miami," TSA Administrator David Pekoske said.
- By Jessica Davis
- Feb 28, 2019

According to a National Retail Federation survey, retailers in the US alone lose almost $50 billion to theft every year.
- By Duane Humphreys
- Feb 28, 2019