
The company, which serves over 1.5 million clients, has been able to get some services back online but is still working to address the damage.
- By Haley Samsel
- Oct 16, 2019

How security teams can improve their defense strategy by integrating bots
- By Gilad David Maayan
- Oct 16, 2019

The health organization realized during an investigation of an August breach that its systems had been breached several times prior to the known attack.
- By Haley Samsel
- Oct 14, 2019

For the third year in a row, SMBs are reporting big increases in the frequency of cybersecurity attacks.
- By Haley Samsel
- Oct 11, 2019

Law enforcement are increasingly worried about the possibility of end-to-end encryption, which does not provide police with a way to access communications between potential suspects.
- By Haley Samsel
- Oct 08, 2019

At a legislative hearing Friday, court administrators answered questions about their decision to hire “penetration testers” who were arrested for burglary last month.
- By Haley Samsel
- Oct 08, 2019

Over 200 accounts were targeted by the group of hackers, but only four were compromised, according to Microsoft.
- By Haley Samsel
- Oct 07, 2019

Even if an organization decides to pay a ransom against the FBI’s advice, they should report the crime to law enforcement, according to the FBI alert.
- By Haley Samsel
- Oct 07, 2019

In the latest ransomware attack scourge, three hospitals in Alabama were able to continue serving existing patients but said they could not take new cases.
- By Haley Samsel
- Oct 04, 2019

The French government plans to introduce a program called Alicem that will require residents to take a selfie video to compare to their passport photo.
- By Haley Samsel
- Oct 04, 2019

Security researchers found 11 significant vulnerabilities in devices that use the IPnet software, though there are no confirmed incidents involving takeovers of the devices.
- By Haley Samsel
- Oct 03, 2019

The Department of Homeland Security is refocusing its efforts on cyber threats to aircraft, and the Air Force is sponsoring “hacking villages” to discover hacking vulnerabilities.
- By Haley Samsel
- Oct 02, 2019

Two of the biggest trends today, particularly in the security surveillance and IoT realms, are border security and the emergence of local governments transforming their communities into smart cities.
- By Kevin Taylor
- Oct 01, 2019
Contractors will face big changes and tight timelines next year when the Defense Department institutes its new Cyber Maturity Model Certification framework
- By Derek B. Johnson
- Oct 01, 2019

Under GDPR, companies can be fined for not having their records in order, not notifying the supervising authority and those affected by a breach, or not conducting an impact assessment.
- By Richard Kanadjian
- Oct 01, 2019
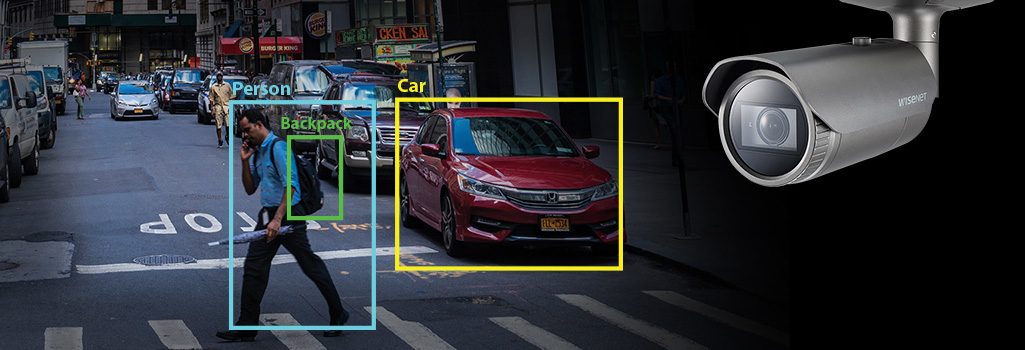
Today, there are in-depth discussions about what ‘might be’ possible with AI, machine and deep learning-based analytics products on the market.

4.9 million users have been affected by the data breach, which DoorDash discovered in the past month.
- By Haley Samsel
- Sep 30, 2019

The chamber also approved funding for the Department of Homeland Security’s cyber arm, with $1 billion dedicated solely to cybersecurity.
- By Haley Samsel
- Sep 27, 2019

The bill is part of an ongoing saga between China-based Huawei and the federal government, which believes Huawei is collaborating with Chinese spying efforts.
- By Haley Samsel
- Sep 26, 2019

The new system may advance the country’s widespread use of surveillance technology in public spaces.
- By Haley Samsel
- Sep 25, 2019