
A new report says some of the top baby monitors are vulnerable to basic hacking attempts.
- By Matt Holden
- Sep 02, 2015

Cloud computing offers numerous benefits, such as powerful processing capabilities, improved access, higher availability and significant savings with on-demand hosting.
- By Amit Cohen
- Sep 01, 2015

From data breaches to security system compromises, there’s a ‘cloud’ hanging over hosted environments, labeling them unsafe or subject to easy compromise.
- By Brian Matthews, Ralph Shillington
- Sep 01, 2015
Updates kiosk inspection protocol to ensure customer data safety.
Technology embedded into core of devices at factory and provides reliable two-way connection.

The ride service is significantly expanding its security team.
- By Matt Holden
- Aug 17, 2015
Collaboration supports and is designed to deliver seamless interoperability.
Partnership enables organizations to easily scan code and eliminate software risk.

Security market to see rise of opportunities in cloud data center security.
- By Ginger Hill
- Aug 12, 2015

Since 2010 high-ranking officials' vacation plans, emails to friends and other correspondence has been targeted by China.
- By Ginger Hill
- Aug 11, 2015
New partnership helps ensure data integrity and operational continuity if a cyber-incident occurs.
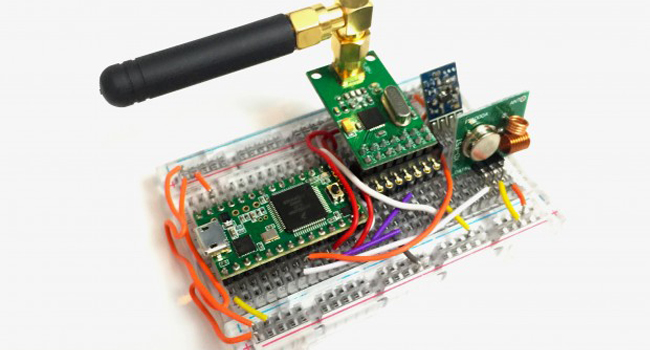
Small $30 device - Rolljam - enables entry into two of your most private places.
- By Ginger Hill
- Aug 10, 2015
Enables monitoring centers to leverage cloud services, including Video Verification, 24/7 Live Intervention, Virtual Guard, Virtual Escort, and Virtual Assistant.
To deliver agentless endpoint security to French market.
Provides common video interface for a wide range of vertical market applications.
Recent hacks expose personal information about millions of people.
- By Alison May
- Aug 06, 2015

Windows 10 features a number of security updates and settings that are important to know, even if you didn’t read the fine print.
- By Matt Holden
- Aug 05, 2015

Some public Wi-Fi hotspots are provided by con artists.
- By Matt Holden
- Aug 04, 2015

Intersecting business into the professionalization of information security debate.
- By Martin Zinaich
- Aug 04, 2015

The funding was led by TPG Growth.
- By Matt Holden
- Aug 03, 2015