ONVIF®, the leading global standardization initiative for IP-based physical security products, has published the Release Candidate for Profile D, a draft specification that covers interfaces for access control peripherals.
Konica Minolta Business Solutions U.S.A., Inc., together with its IT Services division, All Covered, today announced the acquisition of Depth Security, a cybersecurity consulting company that enhances the already impressive and comprehensive security portfolio from All Covered.
Assuming his new role on Oct. 1, Thomas Jensen has been named CEO of Milestone Systems.

TSA security checkpoints to help protect workforce and passengers from COVID-19
HID Global announced that it has acquired Access-IS, a leading technology provider of miniaturized reader devices that combine a number of key technologies ideal for mission-critical environments
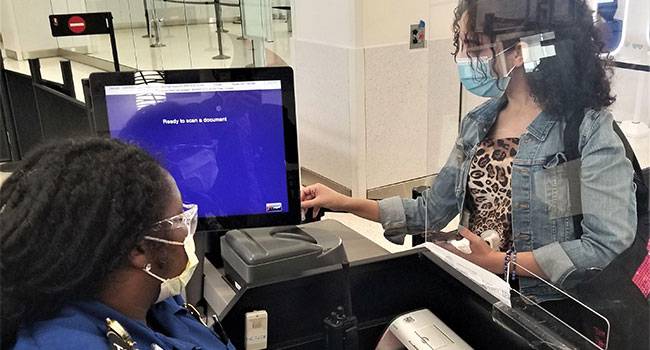
Transportation Security Administration officers at Baltimore/Washington International-Thurgood Marshall Airport and Tampa International Airport are now using new technology that confirms the validity of a traveler’s identification (ID) and confirms their flight information in near real time.
Smarter Security Inc. proudly welcomes a new addition to the Sales team. Bruce Kutsche joins as the company’s senior director of solution sales.
The Transportation Security Administration (TSA) at Austin-Bergstrom International Airport (AUS) suffered the loss of the first-ever passenger screening canine in the state of Texas. Evan, a black Labrador retriever, who retired in August 2017, passed away earlier this month. He was 10 years old.
While public safety has always been at the heart of the smart city movement, the global health crisis has created new security challenges.
Qognify has announced the appointment of Jeff Swaim, as director of channel sales & national accounts, Americas.
Ranking No. 1,639 With Three-Year Revenue Growth of 262 Percent
Senstar is pleased to announce its systems are now successfully integrated with Genetec’s Security Center via Senstar’s Network Manager software.
Allied Universal®, has announced the appointment of Robert J. Wheeler, vice president – Aviation/Maritime Operations for Allied Universal’s National Government Services as Maritime Sector Chief at InfraGard San Diego.
Favorable conclusion reached in patent infringement case; company takes occasion of litigant’s settlement payment to make public its firm stance against nuisance lawsuits from non-practicing entities
Situational Awareness and Enhanced Incident Management Capabilities Complete Transformation to Critical Event Management Provider

Delta Airlines CEO Ed Bastian is reporting that dozens of passengers have been banned from flying with the airline for refusal to comply with the airline industry’s mask policy.
- By Ralph C. Jensen
- Aug 10, 2020
I’m not trying to minimize the worries of that pandemic thing, also known as COVID-19, but there are some interesting things happening the security world, including who is exploring use of new solutions, helping others in need and what’s happening to our trade shows. Here’s a look.
- By Ralph C. Jensen
- Aug 07, 2020
Demonstrations, celebrations, festivals, and major sporting events - any large gathering of people - presents police and security services with a range of issues relating to public safety.
- By Angel Quinn
- Aug 07, 2020