
The inspector general believes D.C.'s transportation system is at a higher risk of cybersecurity attacks.
- By Sydny Shepard
- Apr 30, 2019

Security has been heightened at synagogues in Sacramento following the shooting at a San Diego synagogue Saturday, which left one dead and three injured.
- By Jessica Davis
- Apr 30, 2019

One person died and three others were injured in an shooting on a synagogue in Poway, Calif.
- By Sydny Shepard
- Apr 29, 2019

The readers will record license plate information of vehicles inside BART parking lots when they enter and leave
- By Sydny Shepard
- Apr 29, 2019

There are a number of common misconceptions about endpoint security.
- By Jerry Young
- Apr 29, 2019

Six reasons companies should implement a Zero Trust Security Mode.
- By Michael Sciacero
- Apr 26, 2019

Some common areas and issues to keep growing your business, not your security risk.
- By Gary Brown
- Apr 26, 2019
The second annual summit hosted by ISC Security Events, PSA Security Network and the Security Industry Association will tackle a variety of the latest cyber-physical security trends.

A driver intentionally plowed into pedestrians in California and injured eight people, according to police.
- By Sydny Shepard
- Apr 25, 2019

Four sets of steel bollards have been installed on Memphis' iconic Beale Street as part of a safety improvement plan.
- By Sydny Shepard
- Apr 25, 2019

When it comes to citizen safety, the police cameras in Indianapolis are meant to keep an eye on crime and help catch potential threats.
- By Sydny Shepard
- Apr 25, 2019
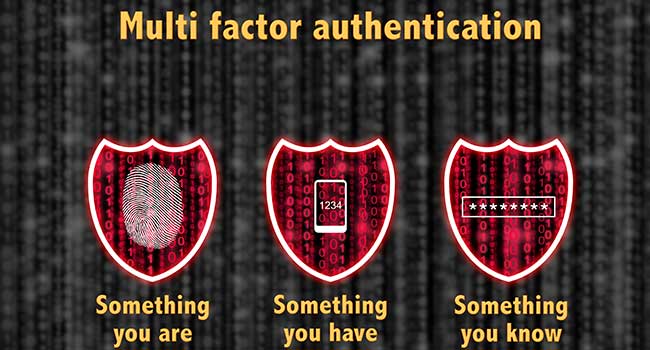
The U.S. Army is working toward adding more authentication measures to provide more options to access Army online resources while maintaining information technology system security.
- By Jessica Davis
- Apr 24, 2019

Beyond user privacy, we’ve seen GDPR impact companies in other ways.

The Chattanooga Police Department has 29 public safety cameras located around the city and plans to add more.
- By Jessica Davis
- Apr 24, 2019
Bee’ah’s sustainable headquarters will be infused with artificial intelligence
across systems and spaces, including a digital concierge for every occupant and visitor
Almost 300 people were killed and hundreds more were wounded in Sri Lanka on Easter Sunday in a series of coordinated attacks that struck three churches and three hotels.

EmCare Inc., a physician-staffing company, says a data breach has exposed personal information for about 31,000 patients
- By Jessica Davis
- Apr 23, 2019

- By Ralph C. Jensen
- Apr 22, 2019