
Attacks on Christmas markets and festivals in 2016 have motivated officials to boost security in order to prevent mass-casualty attacks.
- By Sydny Shepard
- Oct 17, 2017

The hole in Wi-Fi security affects the vast majority of Wi-Fi devices and networks.
- By Sydny Shepard
- Oct 16, 2017

Oops!...Equifax did it again.
- By Chris Olson
- Oct 16, 2017
Total Recall Corporation, a Convergint Technologies Company, will showcase its latest CrimeEye citywide video surveillance solutions.
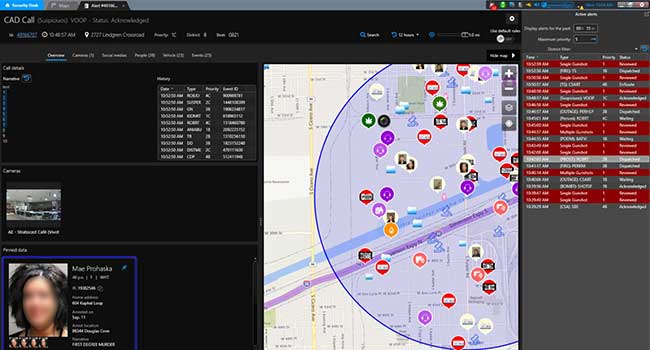
Genetec Inc. announced the launch of its new public safety decision support system, Genetec Citigraf. Created for citywide law enforcement and public safety agencies.

The certification would give the stadium legal protections in the event of a terrorist attack.
- By Sydny Shepard
- Oct 13, 2017
The University offers an array of technical and standards-based information for contractors, integrators, end users and consultants.
Delta Turnstiles announced the second model in its Designer Series of turnstiles - the Sunrise.

According to a new study, 70 percent of employees cannot grasp web security and privacy.
- By Sydny Shepard
- Oct 12, 2017

abode Systems' is expanding features to allow users to build a smart home their own way.
- By Sydny Shepard
- Oct 12, 2017

Dubai International Airport is replacing security checks with an aquarium. Yes, you read that right.
- By Sydny Shepard
- Oct 11, 2017
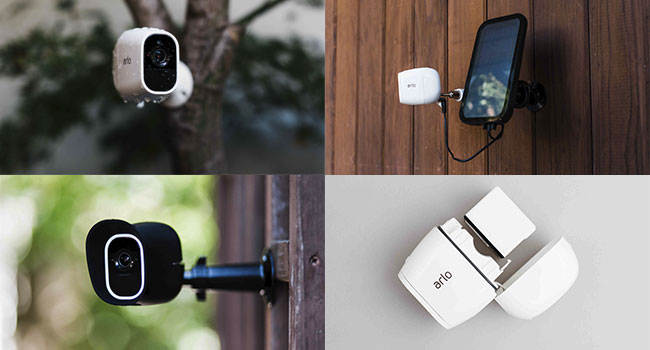
The new Arlo Pro 2 includes HD Video, option 24/7 continuous video recording and a solar power option.
- By Sydny Shepard
- Oct 11, 2017

A shooting at the Texas Tech University Police Department left one officer dead.
DNA Fusion, Schlage LE wireless mortise locks now seamlessly integrate to offer an enhanced, scalable security solution
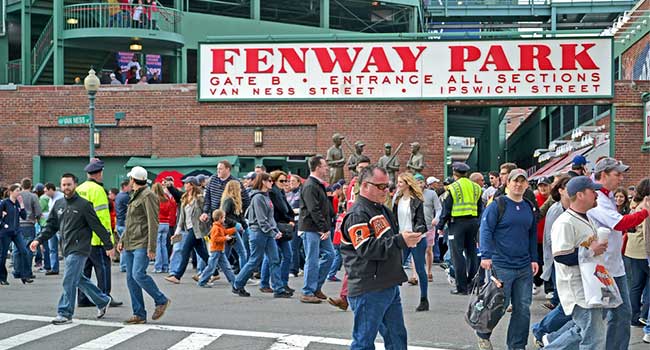
Several sporting arenas boosted security after a lone gunman killed 58 people at an outdoor concert.

Now all electronics bigger than a cell phone must be placed in their own bin.

As organizations seek to adapt to this growing concern, a greater focus is being placed on what a person can do to be safe and how to impart this vital information.