
In an industry increasingly dominated by massive organizations that grow larger with each merger or acquisition, end users find themselves faced with a dwindling number of choices when it comes to selecting a fire, life safety and security integrator.
- By Ann B. O’Connor
- Jul 01, 2017

Securing airports, seaports, railways, bridges and tunnels is no easy task. One technology that transportation agencies are increasingly relying on to secure these environments is thermal imaging.
- By Dwight Dumpert
- Jul 01, 2017

As the 2017 President of ASIS International, it’s my honor to welcome security professionals to Dallas for the ASIS International 63rd Annual Seminar and Exhibits (ASIS 2017) this Sept. 25-28.
- By Thomas J. Langer
- Jul 01, 2017

The Corman Park Police aims to protect and serve its diverse community using the safest and most effective means possible. Its officers work 12-hour shifts, patrolling the community, responding to calls for service and assisting the federal police in criminal offenses and apprehensions.
- By Andrew Elvish
- Jul 01, 2017

More than 750,000 people pass through Grand Central Terminal every day. In addition to operating 24/7, and being one of the most visited tourist attractions in the United States, the terminal is a historic landmark with much of its structure more than 150 years old. These factors presented challenges for the installation of a new video monitoring and services network.
- By Courtney Pedersen
- Jul 01, 2017
For retailers of high end consumer electronics such as smartphones, tablets, e-readers, drones, digital cameras and fitness watches, the customer’s retail experience can be just as important as loss prevention.
- By Del Williams
- Jul 01, 2017
Thriving businesses must continue to grow year over year to survive in the ever-evolving alarm industry. Over the course of a year, products and services change, customer needs evolve and public perception changes with the economy.
- By Lindsay Lougée
- Jul 01, 2017

You are an integrator, and imagine you could have any installation job you wanted. What would you choose? Would it be a well-known company, or a prestigious location? What if you could have both?
- By Ralph C. Jensen
- Jul 01, 2017
Common sense dictates that it is easier to stop something from happening in the first place than to repair the damage after it has been done.
- By Siva G. Narendra
- Jul 01, 2017

Network thermal cameras were first introduced to the security market in 2010 filling a critical detection gap in network video systems.
- By Anthony Incorvati
- Jul 01, 2017

What to look for and how it affects your organization.

The United States has unveiled enhanced security measures for flights to the country designed to prevent a laptop ban.

This summer, the Department of Homeland Security will begin building prototypes for the wall proposed by President Trump on his campaign trail.
The Company Looks to Her to Lead New Branding Initiative
Program Empowers Security Industry Professionals to Enhance Best Practices
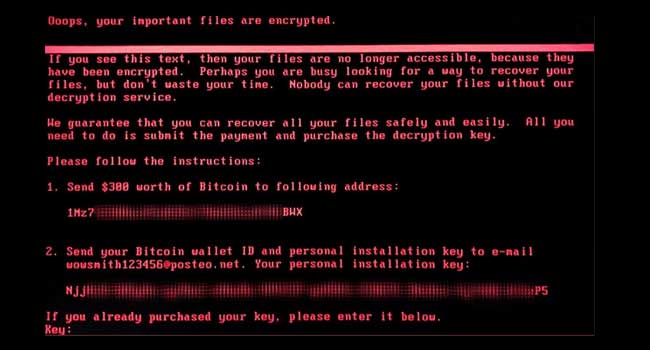
Yesterday, PC users across the world were asking for help as ransomware took data hostage and locked users out of their computers.

See which college campuses top the list of the safest in the United States.

To ensure that new and enhanced systems best meet expectations, one of the most critical steps in the design process is in the initial planning stages
- By Jason Spielfogel
- Jun 27, 2017