Identity, Credentialing and Access Management (ICAM) Laboratory furnished with latest in SAFE Solutions for research/teaching activities.
Providing new options for opening doors and parking gates from a distance.
New integrations include Vingtor-Stentofon, Inovonics, and Bosch.
Version 7.2 includes list search, push notifications in Exacq Mobile, new IP camera integrations and more.

Deadbolt locks provide instant activation and protection.
- By Mark Berger
- Sep 16, 2015

Ahmed Mohamed was detained after his teacher notified authorities.
- By Matt Holden
- Sep 16, 2015

Success found by taking ideas that seemed like sound concepts and putt them into practice in a scalable way.

A new report from Bluebox Security says the top 10 travel apps in the iOS and Android app stores are all riddled with security flaws. Bluebox says encryption app data, insufficient protection against man-in-the-middle attacks, and leftover administration or debugging code are the biggest issues for the iPhone and Android devices.
- By Matt Holden
- Sep 15, 2015
Combines advanced features of security platform with fence detection system.
To unveil exciting new products and also to sponsor ASIS Texas Night at ASIS 2015 in California.

Every level of government developing ways to deal with physical security as well as the data their program produce.
- By Scott Cheatham
- Sep 14, 2015
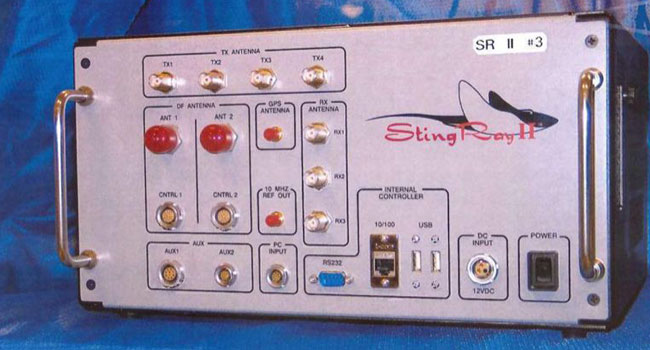
First effort to create uniform legal standards for federal authorities to track cellphones.
- By Ginger Hill
- Sep 14, 2015

Federal Authorities are concerned about security threats against the pope.
- By Matt Holden
- Sep 14, 2015

You might not realize just how much you're actually sharing with complete strangers.
- By Ginger Hill
- Sep 11, 2015

University Hospital, the teaching hospital of San Antonio's University Health Systems is a sprawling campus in the South Texas Medical Center, and one of the health system's 23 locations across the community that needed the latest security technology.
- By Mary Wilbur
- Sep 11, 2015

Number one concern is safety and security balanced with a welcoming, friendly environment for residents, families and visitors.
- By Christopher Hansen
- Sep 10, 2015
His leadership in the security industry had power impacts on the following companies: Hikvision, Panasonic, Samsung Techwin America and SightLogix.
Outlines the stages of public panic and factors and trends influencing these stages.