
The Electronic Security Association (ESA), the national voice for the electronic security and life safety industry, has announced plans to introduce the SECURE Act in state legislatures across the country beginning in 2025. The proposal, known as Safeguarding Election Candidates Using Reasonable Expenditures, provides a clear framework that allows candidates and elected officials to use campaign funds for professional security services.
Viakoo, a leader in vulnerability remediation for IoT, OT, and CPS systems today announced the establishment of the “Cyber Defense Leadership” scholarship at the University of Nevada, Reno. This new program will provide $10,000 to fund an annual scholarship to recognize and nurture the next generation of cybersecurity talent and leadership at the University. With the emergence of new types of threat vectors, including AI-driven threats, more focus on creating next generation security solutions is urgently needed.
The Northborough Police Department (NPD) has become the first law enforcement agency in Massachusetts to go live with the Automated Secure Alarm Protocol (ASAP) Service, a digital alarm service that automates the exchange of alarm information between alarm-monitoring companies and emergency communications centers (ECCs). NPD deployed ASAP View, a web-based solution that enables faster, more accurate alarm delivery directly to emergency communications personnel.
Brinks Home, one of North America's leading smart home security companies, today announced the launch of BHX, a bold new recruiting and sales platform and program designed to attract, develop, and empower the next generation of field sales professionals.
The Security Industry Association (SIA) has named 23 recipients for this year’s SIA RISE Scholarship, a program offered through SIA’s RISE community, which supports the education and career development goals of young professionals and emerging leaders in the security industry.
The Security Industry Association (SIA) has named five women biometrics leaders as recipients of the 2025 SIA Women in Biometrics Awards, a globally recognized program presented by SIA with support from sponsor Leidos, media partner Biometric Update and organizational partners the SIA Identity and Biometric Technology Advisory Board and the SIA Women in Security Forum. The awardees will be recognized at SIA’s 2025 Identity and Biometrics Symposium.
Minuteman Security & Life Safety, the 2025 SDM Systems Integrator of the Year and one of North America’s fastest-growing security and life safety integrators, today announced the acquisition of Life Safety Integrated Systems Inc., a leading systems integrator based in Buffalo, New York.

Ransomware attacks have risen for the first time in six months, increasing by 28% month-on-month to 421 attacks. While overall attack volume remained below 500, the uptick may signal a renewed escalation heading into the year’s most active period for cyber criminals.
Today’s multifamily property owners and operators face mounting challenges: competing with new Class A builds, rising operating costs, capital constraints, compliance risks, and staff burnout. To recognize the dedication of these multifamily property owners and help existing properties reimagine what’s possible, Allegion is launching Operation: Retrofit Refresh Sweepstakes that offers one lucky multifamily property a $20,000 access control overhaul—a turnkey upgrade designed to ease operations, delight residents, and almost-instantly boost NOI.
AMAG Technology is naming Suprema as its strategic partner for biometric readers. This formalized partnership builds on years of successful collaboration and ensures customers worldwide benefit from a fully integrated solution that combines AMAG’s Symmetry™ Solution Suite with Suprema’s biometric technology.
We recently sat down with Paxton’s Chief Commercial Officer Gareth O’Hara to talk about the company’s growth and plans for the US market. O’Hara recently relocated from the UK to the US to help the company’s growth plans.

Trackforce, a provider of security workforce management platforms, today announced the launch of its 2025 Physical Security Operations Benchmark Report, an industry-first study that benchmarks both private security service providers and corporate security teams side by side. Based on a survey of over 300 security professionals across the globe, the report provides a comprehensive look at the state of physical security operations.
Eagle Eye Networks, the global leader in cloud video surveillance, today introduced Eagle Eye Remote Video Monitoring, a security solution that deters crime before it happens. Combining best-in-class AI technology with highly skilled monitoring company professionals, Eagle Eye Remote Video Monitoring detects, intervenes and prevents crime, accelerates police response, and delivers 24/7 protection at a fraction of the cost of traditional security guards.
The Monitoring Association (TMA) is proud to announce that Alan Gillmore, IV, President of Gillmore Security Systems. Inc. has been appointed as TMA’s 38th President. Gillmore assumed the role at the conclusion of TMA’s 75th Anniversary Annual Meeting, held on Wednesday, October 8th, 2025, in Palm Springs, California.
Elite Interactive Solutions, the industry pioneer in remote video guarding and real-time crime prevention, announces the appointment of three key executive roles. The staffing additions come in the wake of the recent private equity investment from CIVC Partners and promotion of Michael Zatulov to CEO. Joining Elite are Jonathan Schwan as CFO, Thomas Stone III as Chief Security Officer, and Eran Yaniv as Vice President of Engineering.

Modern enterprises are grappling with an increasing number of identities, both human and machine, across an ever-growing number of systems. They must also deal with increased operational demands, including faster onboarding, more scalable models, and tighter security enforcement. Navigating these ever-growing challenges with speed and accuracy requires a new approach to identity governance that is built for the future enterprise.
- By Martin Kuhlmann
- Oct 21, 2025
The Security Industry Association (SIA) Women in Security Forum (WISF) has officially launched the sixth annual CAN DO Challenge, a charitable initiative running Oct. 13 through Dec. 3, 2025, designed to unite the security industry in the fight against food insecurity during the holiday season.
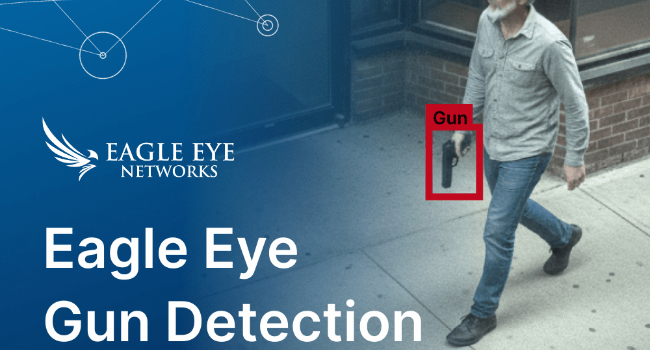
Eagle Eye Networks, a provider of cloud video surveillance, recently introduced Eagle Eye Gun Detection, a new layer of protection for schools and businesses that works with existing security cameras and infrastructure. Eagle Eye Networks is the first to build gun detection into its platform.