HID, a provider of in trusted identity solutions, announces the acquisition of ZeroSSL, an SSL certificate provider based in Austria. The acquisition will not only augment HID’s capabilities in providing protected communications to and from websites, but also strengthen its reputation as a leading provider of trusted PKI solutions.

When done right, collaborative efforts among public law enforcement agencies and private security businesses can profoundly impact crime.
- By Keith Bushey
- Jan 09, 2024

Known for its pioneering work in network technology, Axis Communications enables a smarter and safer world by creating solutions for improving security and business performance. To prove this, Axis conducted an experiment where they explored the limitations of their own technology. They did this by deploying one of their cameras in the most unexpected place – underneath the ice in an ice hockey rink.
Melvin Bradley Kamcheff, better known as Brad, was a 35-year employee of Aiphone Corp. who led the company’s marketing team and was instrumental in developing the company’s strategic marketing plan. Sadly, Brad passed away unexpectedly on Dec. 26th, 2023, at his home in Kirkland, Wash. He was 54 years old.

Genetec Inc., a provider of unified security, public safety, operations, and business intelligence solutions, announced that the Fort Lee, New Jersey Police Department has modernized its automatic license plate recognition technology (ALPR) with Genetec AutoVu™ Cloudrunner vehicle-centric investigative system.

Classes have been canceled at Perry High School, Iowa, as well as students dismissed from other K-12 facilities after an armed attacker opened fire inside a rural Iowa high school on the first day back from winter break Thursday morning. At least one student is reportedly dead from the shooting.
- By Ralph C. Jensen
- Jan 04, 2024
ONVIF, the open industry forum supporting standardized communications between IP-based physical security products, recently announced an agreement with the Open Security & Safety Alliance (OSSA) to take over the development of data ontology and metadata specifications. The initiative will continue under a new ONVIF metadata working group.

Netwrix, a cybersecurity vendor that makes data security easy, recently revealed additional findings for the financial, banking and accounting sector from its survey of 1,610 IT and security professionals from more than 100 countries. According to the report, within the last 12 months, 77% of financial organizations detected a cyberattack, compared to 68% among other industries. Phishing and ransomware were the most common types of attacks across all sectors.
The security industry is forecasting a strong 2024, according to the results from the latest Security Industry Association (SIA) Security Market Index.
Hytera, a provider of innovative communication solutions, announces the launch of the Hytera PNC560, a groundbreaking Push-to-Talk over Cellular (PoC) radio, handheld smart device, and scanner designed to revolutionize nationwide business operations and remote workforce communications. PoC provides instant and secure nationwide communications at the push of a button.
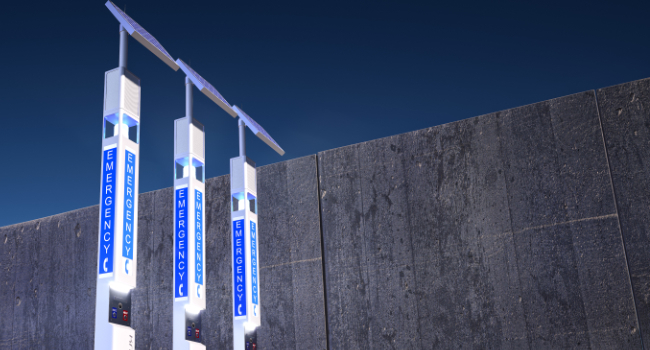
Knightscope Inc., a developer of autonomous security robots and blue light emergency communication systems, today announces an expansion contract for 3 K1 Blue Light Towers with a public transportation provider located in Texas, bringing the total number of Towers purchased to 13. In addition, contracts for the Knightscope Emergency Management System (“KEMS”), a full-service maintenance program and a 2-year voice and data plan were signed to cover all 13 devices.
The Security Industry Association (SIA) has named Renee Thompson – director of global sustainability and environmental compliance at Wesco International – as the first-ever chair of SIA’s Environmental, Social and Governance (ESG) Advisory Board.

Axiad, a provider of organization-wide passwordless orchestration, today announced the results of its 2023 State of Authentication Survey. The survey investigated the types of cyberattacks respondents were most afraid of and prepared for, how their organizations held up against password-based attacks, if and why companies are still using passwords, and what cybersecurity technologies companies plan to use in 2024.
i-PRO Co., Ltd. (formerly Panasonic security) a provider of professional security solutions for surveillance and public safety, today shared its top four predictions for the physical security industry in 2024.

Data is the lifeblood of effective physical security measures. The ability to gather, store and analyze video surveillance data is essential for safeguarding people and places.
- By Vishwa Vijoyendra Narayan
- Dec 21, 2023
The process of disclosing security vulnerabilities is an unpredictable quagmire. It is a process that, by necessity, starts off on a confrontational note. The first message sent from a security researcher to an organization is almost always bad news of some sort, and the organization now has a problem to understand and respond to.

Electric Utilities worldwide face a range of risks and threats, including at the physical perimeters of their highly distributed operational sites. Security professionals grapple with challenges related to sourcing cost-effective and highly efficient physical security solutions to protect operational continuity, invaluable assets, and staff.
- By Kevin Wine
- Dec 19, 2023