
Cincinnati prepares for safety at Great American Ball Park for the 86th edition.
- By Ginger Hill
- May 04, 2015

The fierce competition in the hospitality market has created a need to think creatively in order to increase the number of visitors. Therefore, Copenhagen Zoo constantly looks for new ways to give their customers an interesting and out-of-the-box experience.
- By Courtney Dillon Pedersen
- May 01, 2015
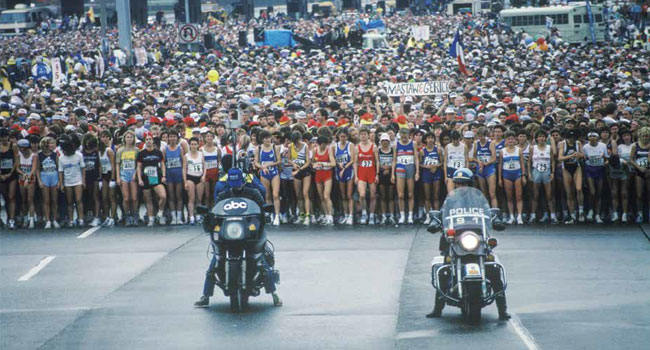
The 2014 TCS New York City Marathon was first held in 1970 by the New York Road Runners Club (NYRR) with just 127 competitors running loops around Central Park.

Public safety leaders from Indianapolis will gather today to discuss plans for the Final Four
- By Matt Holden
- Mar 31, 2015
Company's North American footprint continues to grow.

After a riot broke out on campus two years ago, the University of Dayton is poised and ready to create a safe environment.
- By Ginger Hill
- Mar 13, 2015
AHA picks-up APC, Catalyst Wire & Cable, ClearView CCTV, Dropcam, EnGenius, IC Realtime, Nest, Rapid Mounts, TiVo and Vivitek lines.
Looking forward to serving customers and exceeding their expectations.

With an underground bunker, LAPD officers, FBI, Department of Homeland Security and snipers, yearly award ceremony went off without a hitch.
- By Ginger Hill
- Feb 23, 2015

The government is also looking to prevent young people from becoming radicalized.
- By Matt Holden
- Feb 19, 2015

The NFL will add security to watch over the balls
- By Matt Holden
- Jan 30, 2015

Government agencies team up to ensure players, coaches, staff and attendees are safe and secure.
- By Ginger Hill
- Jan 28, 2015

The Southern California security guard was considered a hero by many
- By Matt Holden
- Jan 05, 2015
It is based on the chocolate shop hostage incident in Sydney, Australia, on Dec. 15.

The victim is a state caseworker
- By Matt Holden
- Nov 19, 2014

An unidentified man was able to get access to a secure area backstage at an appearance by the president
- By Matt Holden
- Oct 06, 2014
The new Boston One Campus will serve as Schneider Electric’s new North America Headquarters and hub for innovation and efficiency.

As the season gets underway, stadiums are taking some new security measures
- By Matt Holden
- Sep 05, 2014

- By Matt Holden
- Aug 11, 2014

According to data from the American Public Transportation Association, riders took a staggering 10.7 billion trips on public transportation in 2013, marking the eighth year in row that more than 10 billion trips were taken on public transportation systems nationwide.
- By Greg Peratt
- Jul 01, 2014