Morse Watchmans ISC West Exhibit Showcases Key Management Technology
This week at ISC West, Morse Watchmans is demonstrating a variety of offerings that highlight their industry leading key control technology. Used in applications ranging from schools to museums to casinos and from hospitals to correctional facilities, Morse Watchmans key control and management solutions help improve operational security by providing comprehensive safeguarding and management of keys.
 Features such as scheduled reports, automatic email notifications, key reservations, mobile capability and now key ring inventory demonstrate how Morse Watchmans key control solutions are evolving to be even more powerful and purposeful in an overall security strategy. These and other innovative key control solutions on display demonstrate Morse Watchmans’ capabilities in providing state-of-the-art security solutions for key control and asset management.
Features such as scheduled reports, automatic email notifications, key reservations, mobile capability and now key ring inventory demonstrate how Morse Watchmans key control solutions are evolving to be even more powerful and purposeful in an overall security strategy. These and other innovative key control solutions on display demonstrate Morse Watchmans’ capabilities in providing state-of-the-art security solutions for key control and asset management.
“Our product line has established itself as the go-to solution for key control systems because of its reliability and proven capability to reduce risk exposure,” said Fernando Pires, VP Sales and Marketing, Morse Watchmans. “The ongoing refinements and upgrades to product features and functionality ensure we stay current with customer needs, while underscoring our understanding and knowledge of the market.”
Featured products include the following:
KeyWatcher Touch offers the convenience of scheduled PDF reports that are automatically emailed to authorized recipients. Email delivery of customized or standard reports can be scheduled for any frequency or specific time, or they can be accessed using the Morse Watchmans smartphone app. System administrators have access to view or run reports as needed. The system also enables security management to easily notify a user via email when a key becomes overdue.
KeyWatcher TrueTouch software has been updated to incorporate key ring inventory functionality. Now, multiple rings can be designated for a single SmartKey, allowing users to more easily define what keys and rings are attached to the SmartKey. The advanced TrueTouch software runs all programming, remote functions and reports for all KeyWatcher Touch locations, while the server synchronizes transactions and maintains the SQL database. Both access control systems and customized client control software interface with the server application.
KeyWatcher Illuminated can be configured with a variety of modules and customized to specific user needs. Available modules include the credit/access card module and single and dual locker modules, which can be used in any KeyWatcher system to hold small valuable items.
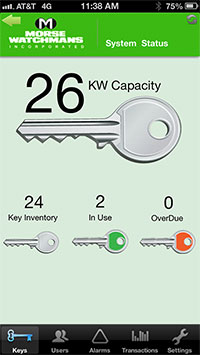 Morse Watchmans’ Mobile App enables authorized users to see a wide range of live information and to interact remotely with the KeyWatcher Touch key control and asset management system. It’s a highly efficient and easy to use tool that greatly simplifies key control management while on the go.
Morse Watchmans’ Mobile App enables authorized users to see a wide range of live information and to interact remotely with the KeyWatcher Touch key control and asset management system. It’s a highly efficient and easy to use tool that greatly simplifies key control management while on the go.
Also on display are the KeyBank Key Control System that provides total accountability of large quantities of keys; KeyPro Software; KeyRings; PowerCheck Guard Tour System and TourPro Data Sorting Software.