
DNS leaks can be a surprisingly common issue and are often only noticed when actively looked for.

Since each insider threat is very different, preventing them is challenging.
- By Tim Matthews
- Mar 19, 2019

What does the future hold for audit and compliance?
- By Simon Hill
- Mar 18, 2019

Despite their new image as a failed cybersecurity company, Equifax is warning Canadians to do more to protect their data.
- By Sydny Shepard
- Mar 15, 2019

A survey found that security professionals are making the move to biometrics, but that they could be doing more to protect data.
- By Sydny Shepard
- Mar 15, 2019

More than 600,000 Michiganders may have had their information compromised by a data breach of several major health care systems.
- By Jessica Davis
- Mar 12, 2019

“I believe the future of communication will increasingly shift to private, encrypted services where people can be confident what they say to each other stays secure and their messages and content won't stick around forever. This is the future I hope we will help bring about,” Zuckerberg wrote.
- By Jessica Davis
- Mar 08, 2019

Verizon takes its Data Breach Investigations Report and refocuses on Insider Threat reports.
- By Sydny Shepard
- Mar 06, 2019

Facebook users have found that a phone number they added to their account for the sole purpose of two-factor authentication can be used to look up their account by advertisers and strangers.
- By Sydny Shepard
- Mar 06, 2019

“We found that you could break out of the kiosk and interact with the underlying Windows operating systems, and from there do things like drop malware or open up the database,” said Daniel Crowder, research director at the IBM X-Force Red security unit.
- By Jessica Davis
- Mar 05, 2019

What can you do to protect your personal data in 2019?
- By John Heath
- Mar 05, 2019

TikTok, a popular video-sharing app, has agreed to pay $5.7 million to settle allegations that it collected data on children.
- By Sydny Shepard
- Mar 04, 2019

Back when IT was dominated by on-premises data centers, storage options were fairly straightforward and securing storage resources was relatively simple compared with today’s far more complex storage landscape.
- By Richard Diver
- Mar 01, 2019
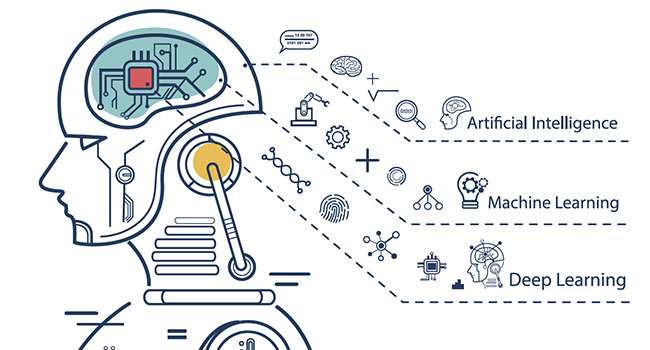
The past few years have seen significant advancements in computing power. With this, machines seem to have a greater ability to learn about us and participate in our lives.
- By Sean Lawlor
- Mar 01, 2019

Millions of video surveillance cameras around the world are losing money.
- By Scott Seraboff
- Mar 01, 2019
People are always trying to predict industry trends, but virtually all of the predicted trends I have read lately are just a subset of the benefits offered by cloud managed video.
- By Richard Sheppard
- Mar 01, 2019

5G is the talk of the town, but is it free of security risks?
- By Sydny Shepard
- Feb 27, 2019

The Defense Department website used to transfer large files containing sensitive unclassified information was brought back online earlier this month after being taken down due to security concerns last year.
- By Sydny Shepard
- Feb 27, 2019

McAfee's Mobile Threat Report found that reporting backdoors, malicious cryptomining, fake apps and banking Trojans all increased substantially in 2018.
- By Sydny Shepard
- Feb 26, 2019
Reverse engineering is a powerful tool to keep in your cybersecurity tool belt.
- By Dennis Turpitka
- Feb 26, 2019