
Cybersecurity experts expect there will be more people falling victim to the worldwide cyberattack that hit on Friday.

Several British Hospitals say they are experiencing major computer problems as the result of a breach in cybersecurity.

President Trump has signed an executive order to strengthen the government’s cybersecurity.

The Transportation Security Administration has laid out new framework to protect soft targets in airports as well as consider electronics ban on flights from Europe.

Just days ahead of the French Presidential Election, candidate and now France’s president-elect announced his campaign had been hacked.

It’s time to take the pledge to improve your password habits.

Don't edit that Google Doc, at least not today.
The IT approach to layered security for systems, infrastructure and data is increasingly impacting the security department, and with good reason.
- By Jeff Whitney
- May 01, 2017

Chipotle customers may have more to complain about than just an extra cost for guacamole.

Uber knows where to find you even if you do delete the app.

In recent years a disturbing new trend is on the rise – cybercrime relating to tax returns and tax-related data. For its victims, Tax Day represents inconvenience and loss.
- By Ebba Blitz
- Apr 18, 2017

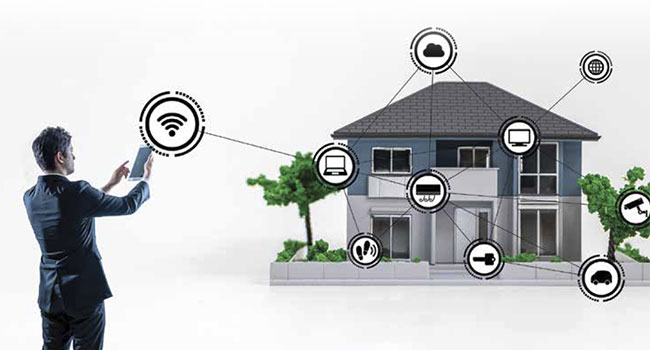
This age of connectivity is the age of possibility, and millions of people all over the world are taking advantage of the wonderful benefits these devices have to offer.

The ability to integrate data from disparate sources in order to analyze and make sense of it is not only key to doing business today; it’s the difference between a company’s success and failure.
- By Caio Milani
- Apr 13, 2017

How to Prevent Breaches, Not Just Clean Up the Mess
- By Steven Minsky
- Apr 10, 2017

Interface Security Systems (ISS) is a cloud-based managed security services provider. The company integrates network and security needs into one platform, with the goal of being a singlevendor source for their customer’s needs.
- By Tiffany Coles, Tori Martinez
- Apr 01, 2017

The live webpage will frequently update with content from the show floor.
- By Matt Holden
- Mar 23, 2017

Regardless of term, or use case, it’s well-known that cybercriminals can hack into any vulnerable device connected to the internet to remotely take control of that device and enslave it into a botnet that is part of a distributed denial-of-service (DDoS) attack.
- By Stephanie Weagle
- Mar 22, 2017

Over the weekend, Saks Fifth Ave reported that customers’ data may be exposed.

In a hearing with the Intelligence Committee, FBI Director James Comey said there was no evidence to support President Trump’s tweets claiming Trump Tower was wiretapped by former President Obama.

We have failed to focus on what’s most important: building security in.
- By Peter Hesse
- Mar 20, 2017