SureView Systems welcomes Hedrick Godisan as a Systems Engineer for the US CS/Guard Force division, bringing a wealth of technical project and back-end IT systems management experience to the team.

The department faced outcries of support for mandatory body cameras and dashcams after two black men were killed by police officers within two years.
- By Haley Samsel
- Sep 05, 2019
LifeSafety Power Inc., a company founded in 2009 has been acquired by ASSA ABLOY Group. The acquisition took place Sept. 5.
Valerie Anderson to lead Boon Edam Inc. in driving sales and customer satisfaction in the Americas.

The laws allow Texans to carry guns into houses of worship unless explicitly banned and clear gunowners to carry firearms on their person for a full week after a natural disaster is declared.
- By Haley Samsel
- Sep 04, 2019

The gunfire occurred shortly after a woman was struck by a car near the fairgrounds and police officers responded to St. Paul’s fifteenth homicide of 2019.
- By Haley Samsel
- Sep 04, 2019

After shootings in El Paso, Texas and Southaven Mississippi, Walmart’s CEO says it will stop selling handguns completely and ask customers not to openly carry their firearms in stores.
- By Haley Samsel
- Sep 03, 2019

Information mishandling, snooping and location tracking are often the ways in which users find their privacy violated online.
- By Susan Alexandra
- Sep 03, 2019

Facing criticism over low voter turnout and barriers to caucusing, party officials planned for remote caucuses in 2020. But the national Democratic Party said the methods would expose the process to high cybersecurity risks.
- By Haley Samsel
- Sep 03, 2019
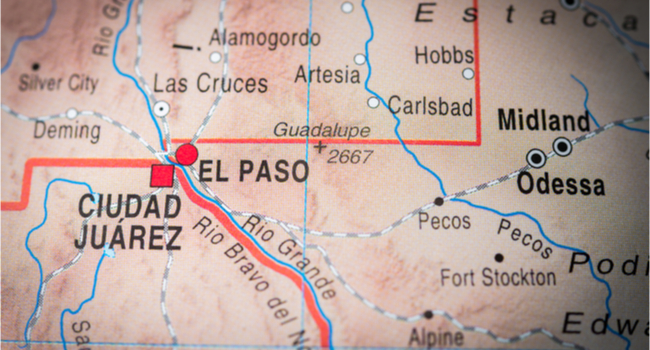
Seth Ator, 36, went on a deadly shooting rampage from Midland to Odessa, Texas on Saturday. Ator fatally shot 7 and injured 22 in the shooting spree.
- By Sherelle Black
- Sep 02, 2019
Keynotes, booths and sessions that you don’t want to miss at GSX 2019 in Chicago from Sept. 8 to 12
- By Haley Samsel
- Sep 02, 2019
I’m a pretty lucky guy. I get to drive to work with my best friend. Each day when I drop my wife off at her office I am hopeful that everything is OK when she goes into her office.
- By Ralph C. Jensen
- Sep 01, 2019

The Internet of Things continues to grow, offering new possibilities for organizations to communicate messages and automate processes. This can be especially helpful when dealing with safety issues.
- By Pat Scheckel
- Sep 01, 2019

The number and breadth of devices that make up the Internet of Things (IoT) continues to grow rapidly, with everything from kitchen appliances to video surveillance and access control systems offering the ability to connect to a network.
- By Ryan Zatolokin
- Sep 01, 2019

We know by now that there is an abundance of business advantages in the cloud — it’s agile and cost-efficient, and, with little to no hardware maintenance, it’s easier to update and perform maintenance on than traditional on-site servers.

A new IT trend–“hyperconvergence”–may hold the key to simplifying this task while also enabling significantly more sophisticated ways to tap the value of data many organizations are already collecting.
- By Eric Bassier
- Sep 01, 2019

The world is quickly urbanizing, and people are flocking from suburbs and rural areas to cities more than ever before.

To ensure continual patient care and remain compliant with regulations, hospitals have well-documented security protocols and deploy technology to ensure those can be executed smoothly, from cybersecurity solutions on the digital side to video surveillance and door scanners, among other tools, on premises.
- By Noah Reiter
- Sep 01, 2019