
The rise in active shooter incidents and the escalating impact of hostile events has prompted the National Fire Protection Association to process NFPA 3000, Standard for Preparedness and Response to Active Shooter and/or Hostile Events, as a provisional standard, which means it would be available for use as early as April 2018.
- By Jessica Davis
- Jan 10, 2018
Talkaphone is excited to announce it is joining forces with two prominent Midwestern private equity funds

CES organizers added vehicle blockades, more armed security and other safety measures for the giant tech trade show.
- By Sydny Shepard
- Jan 09, 2018
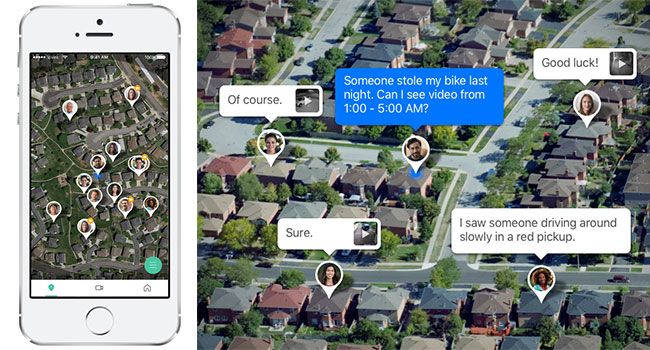
Vivint has introduced a free app called, "Streety" which allows neighbors to share live video feeds from their home security cameras.
- By Sydny Shepard
- Jan 09, 2018
Last week, two major security flaws were discovered in the microprocessors inside nearly all computers.
- By Sydny Shepard
- Jan 09, 2018
ISC West will debute its SIA Education@ISC session lineup for the 2018 show in Las Vegas in April.
- By Ralph C. Jensen
- Jan 08, 2018

It seems that Uber is still learning from its mistakes, even as it continues to grow at a rapid rate. But for other companies, the security breach provides a few key lessons.
- By Matthew Walker Jones
- Jan 08, 2018

Last Tuesday, college and university presidents across Florida received a 1,250-word extortion email threatening violence.
- By Jessica Davis
- Jan 08, 2018
Securitas is strengthening its global position in 2018.
- By Ralph C. Jensen
- Jan 08, 2018
ADT, located in Boac Raton, FL, is going public again.
- By Ralph C. Jensen
- Jan 05, 2018

Use of personal cellphones by White House staffers and guests will be banned in the West Wing, the Trump Administration said Thursday.
- By Jessica Davis
- Jan 05, 2018

Atlanta Police say they are working with the United States Secret Service to create a comprehensive security plan for Monday's College Football Playoff National Championship due to President Donald Trump’s expected attendance.
- By Jessica Davis
- Jan 05, 2018

The vulnerabilities, which were originally believed to only be in Intel chips, affect a variety of chip vendors and could allow hackers to steal the entire memory contents of computers, mobile devices and services running in cloud computer networks.
- By Jessica Davis
- Jan 04, 2018

Before you go wading into all your unread emails from over the holidays, it’s a good idea to brush up on phishing email scams, which can lead to financial loss, compromised accounts, identity theft, ransomware infection and insecure data.
- By Jessica Davis
- Jan 04, 2018

A man fired more than 100 rounds at sheriff’s deputies in Colorado early Sunday, killing one officer and injuring four others and two civilians before being fatally shot himself.
- By Jessica Davis
- Jan 03, 2018

New York City is set to install more than 1,500 new permanent traffic bollards in public spaces around the city to help protect pedestrians and prevent against vehicular attacks, Mayor Bill de Blasio announced Tuesday.
- By Jessica Davis
- Jan 03, 2018

As we enter 2018 and desire to protect both our own personal digital assets as well as critical corporate data, it is useful to examine the anticipated key trends in cybersecurity in 2018.
- By Ebba Blitz
- Jan 02, 2018
Even Mother Nature couldn’t turn the tide when CG&E Systems Group stepped into the security integration market. You remember Hurricane Irma, right? Well, both happened about the same time, and the winner is … CG&E.
- By Ralph C. Jensen
- Jan 01, 2018