The global access control market is forecast to be worth nearly $10 billion by 2022, with annual growth nearing 7.5 percent over the next six years, according to a recent report by Markets and Markets Research firm.
- By Karen Evans
- Jan 01, 2018
The New Hampshire Liquor Commission (NHLC) experienced a record-breaking fiscal year in 2016. With the increase of business, and the addition of three more state-run stores, the state commission felt it was time to improve on security solutions. Enter Griffon Security Technologies.
- By Ralph C. Jensen
- Jan 01, 2018

The concept of “securing security” emerged when physical security was being affected by cybersecurity attacks.
- By Lance Holloway
- Jan 01, 2018
A few years ago – three to be exact – I became the legal guardian of a granddaughter, and with that came the finding of a daycare that not only provided a good learning environment, but a haven of safety and security.
- By Ralph C. Jensen
- Jan 01, 2018
Physical security systems continue to migrate to the network, enabling overall better integration, performance and improved total cost of ownership. Nowhere is this more evident than with the proliferation of IP cameras.
- By Ronnie Pennington
- Jan 01, 2018

Stadium security has gotten a lot more complicated than apprehending seat jumpers, defusing confrontations and ejecting rowdy fans for imbibing one too many beers.
- By Mark McCormack
- Jan 01, 2018

As technologies and laws continue to evolve and more people move into urban centers, cities are looking for ways to become smarter — and safer.
- By Pota Kanavaros
- Jan 01, 2018

In the wake of multiple terror attacks and mass shootings this year, some of the biggest New Year’s Eve celebrations in the United States are increasing their security.
- By Jessica Davis
- Dec 29, 2017

In 2018 we can expect to see continued creativity from nation-state actors, a growing focus on industrial control systems, and efforts to compromise the software supply chain.
- By Toni Gidwani
- Dec 28, 2017

The solution is in hand, literally. It’s the mobile phone.
- By Dr. Sarbari Gupta
- Dec 27, 2017

- By Dmitri Alperovitch
- Dec 26, 2017
This holiday season, however, after a year of nasty data breaches, it feels appropriate to take Dr. Seuss’ How the Grinch Stole Christmas[2] and analyze it with some of the basic questions we ask during a data breach.
- By Tyler Reguly
- Dec 22, 2017

Occly proves that you can have total personal and home security with just one device.
- By Sydny Shepard
- Dec 22, 2017

As we look back on these security events, think of how we can move forward to predict and prevent incidents like this in the future.
- By Jessica Davis
- Dec 21, 2017
There are some relatively easy solutions to keeping your home safe and secure while you’re away enjoying the holiday festivities.
- By Herman Yau
- Dec 21, 2017
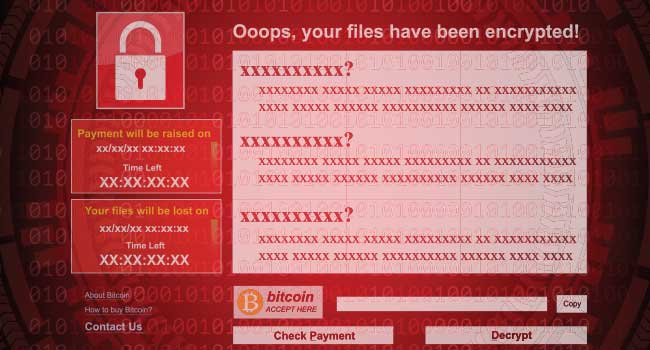
The White House has publicly blamed North Korea for the WannaCry ransomware attack earlier this year that locked more than 300,000 computers in 150 countries.
- By Jessica Davis
- Dec 20, 2017

The DHS’s Science and Technology Directorate “Securing Mobile Applications for First Responders” report said that security flaws were discovered on 32 of the 33 popular apps tested.
- By Jessica Davis
- Dec 20, 2017

President Trump declared a new national security strategy in a document and speech on Monday, focusing on “America First.”