With the holidays upon us, there is no better time to start implementing these safety measures.
- By Patrick V. Fiel, Sr.
- Dec 05, 2016
Security Experts to Lead the Development and Integration of Physical Security Information Management (PSIM) System in Support of State Department’s Worldwide Upgrade

SWAT teams were able to break into the bank to rescue hostages and arrest the suspect.

Close the door on Locky ransomware infection via Facebook
- By David Biser
- Dec 02, 2016
Nuccio joins ADT from ASG Security, where he served as President and CEO.
CBC LightGuard Action Camera Recorder Named as Attendee’s Choice for Featured Product Showcase at ISC East

This year marks the 20th anniversary of the world’s first IP network camera, a technology that eventually revolutionized the video surveillance landscape.
- By Fredrik Nilsson
- Dec 01, 2016

If these technologies aren’t on your radar, they probably should be. These product categories are rapidly growing in popularity and for good reason.
- By Brian Carle
- Dec 01, 2016
It’s an exciting time to be in the security industry, as evidenced by the successful year we have seen in regards to technology innovations, mergers and acquisitions, and a renewed sense of pride in the industry.
- By Sharad Shekhar
- Dec 01, 2016
There are myriad clichés that describe change. However, the one that seems to suit Security Products magazine best is: Success is often brought about by change.
- By Ralph C. Jensen
- Dec 01, 2016

When the Olympic Games come to town, the welfare of people and property are of paramount importance in both the planning process and during the event.
- By Raleigh Gerber
- Dec 01, 2016
There is an old saying about how everything is bigger in Texas, and in the case of Lexus of Lakeway, the expression certainly rings true.
- By Steve Birkmeier
- Dec 01, 2016

What’s ahead in 2017? In 2016, we saw video surveillance and security increasingly become the focus of mainstream media conversations, with video playing a pivotal role in bringing terror suspects to justice (as it did recently in NYC) and with police body-worn cameras capturing sometimes controversial incidents that spark national conversations.
- By Wayne Arvidson
- Dec 01, 2016

Provides needed training and CEUs for the security industry with over 125 courses.
Company to provide discount on residential security services for members of prominent non-profit.
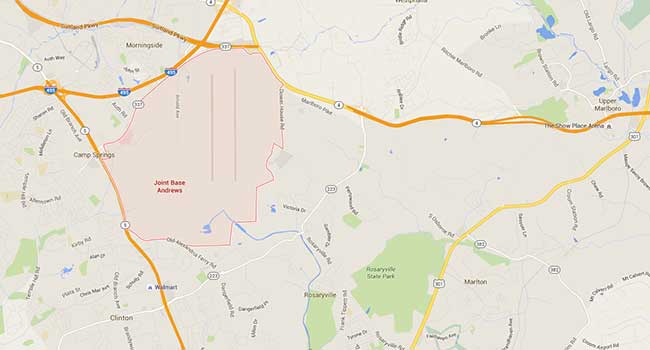
Joint Base Andrews in Maryland has been placed on lockdown following a report of an active shooter.
- By Sydny Shepard
- Jun 30, 2016

Each of these four key components are essential in establishing a solid defense against would-be cyber-attacks.
- By Gabby Nizri
- Jun 29, 2016

41 died and more than 230 more were injured when three men open fired and set off explosives at a Turkish airport.
- By Sydny Shepard
- Jun 29, 2016