Video Surveillance Solutions from Dahua Now Available in 103 ADI Store Locations throughout the US and Canada.

Afghan police are reporting an explosion that killed dozens and left hundreds wounded.
- By Sydny Shepard
- Apr 19, 2016
Funds Raised at ISC West 2016 to Benefit Children in Need
Orion Entrance Control, Inc. will showcase the latest technology in turnstiles and lane control software at the 26th annual ASIS NYC Security Conference and Expo.

It’s been three years since a terrorist attack plagued the Boston Marathon, but authorities are not letting up on keeping the runners and spectators safe.
- By Sydny Shepard
- Apr 18, 2016

The United States and Russia are meeting to discuss cybersecurity, and hopefully prevent a cyber war.
- By Sydny Shepard
- Apr 18, 2016

Belgian Transit Minister, Jacqueline Galant, resigned after it was leaked that she ignored found security lapses in the Brussels airport.
- By Sydny Shepard
- Apr 15, 2016
New RLGE2FE16R designed to prevent unauthorized network access.

Microsoft filed a lawsuit against the U.S. Department of Justice taking a stand against the way federal agents routinely search its customers’ personal information in secret.
- By Sydny Shepard
- Apr 15, 2016

Coachella, a music festival in Indio, California, will be seeing an increase in security measures due to recent world events.
- By Sydny Shepard
- Apr 15, 2016
Washington State’s most populous county integrates emergency notification, video surveillance and access control systems with single-user interface solution.

Based on research done by Intel Security, there is a c-level blind spot when it comes to the vulnerabilities of the cloud.
- By Sydny Shepard
- Apr 14, 2016
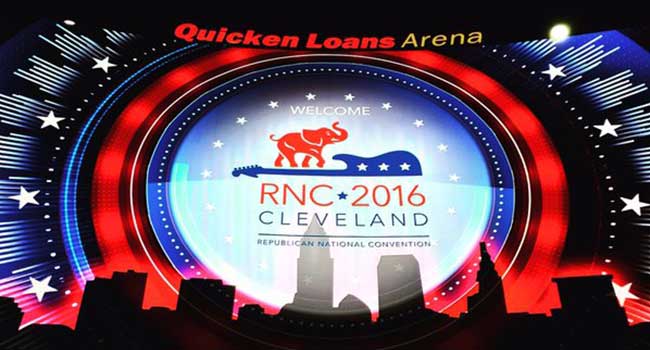
Cleveland is spending $20 million in federal money on riot and security gear for the Republican Convention.
- By Sydny Shepard
- Apr 14, 2016

Fans of the college basketball tournament, March Madness, may need to pay special attention to the information they shared on the CBS Sports app and website during the popular event.
- By Sydny Shepard
- Apr 13, 2016

- By Matt Holden, Sydny Shepard
- Apr 12, 2016
When I attend ISC West next year, I’ll be better prepared.
- By Sydny Shepard
- Apr 12, 2016

This year at ISC West in Las Vegas, there were some definite trends to be seen in the security industry.
- By Sydny Shepard
- Apr 12, 2016
The last day of ISC West saw some unexpected and innovative products
- By Matt Holden
- Apr 12, 2016