What is Wrong With This Picture?
New anomaly detection technology transcends conventional video analytics
- By Ken LaMarca
- Dec 05, 2022
Recently, the industry has been buzzing about video analytics technologies. The talk is about how they have the intelligence to help prevent potentially threatening events from escalating, and even proactively detect threats before they take place. This is undoubtedly a game changer for physical security and law enforcement professionals looking for effective ways to reduce crime and enhance overall security.
Video analytics also provide security professionals with the long-awaited solution they need to substantiate the budget for more advanced security technologies. This has always been a challenge without demonstrating how such investments deliver real return on investment (ROI). Given the wide range of security and business intelligence applications across the enterprise, and relative ease of deployment for most solutions, video analytics can more easily be cost-justified.
However, legacy video analytics technologies have a fundamental limitation: they are rules-based solutions that detect only what they are programmed to see, requiring the use of application-specific software modules. This can be costly to implement and inefficient in detecting events that require action.
For example, if you employ an analytic solution that autonomously detects weapons, and a fight breaks out, the latter will go undetected. Unless staff who spot the fight and take immediate action are monitoring the video system, the event will go unnoticed until reported – at which point the situation may be critical.
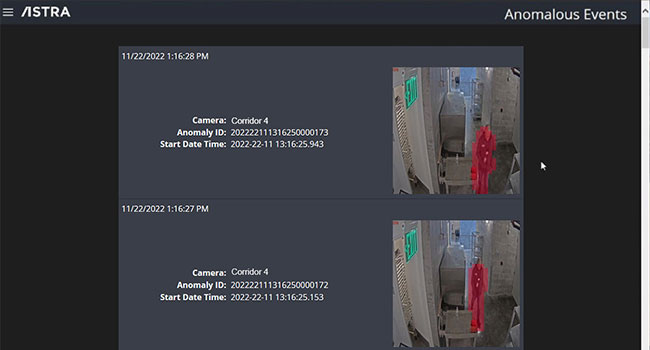
All this has changed with an emerging technology that goes far beyond the capabilities of traditional video analytics solutions – Anomaly Detection. Anomaly detection employs machine-learning algorithms that continuously adapt to events in a specific surveilled area. If something as simple as a person falling or laying on the ground occurs in an area where this type of event is statistically uncommon, the technology detects the event in real-time and alerts designated personnel or first responders.
This applies to any abnormal activity that takes place in the designated camera’s field of view – unruly crowds, fire and smoke, fighting, weapons brandishing, irregular movement of vehicles or people, vandalism, or anything that is simply not supposed to be taking place in a given area.
Anomaly detection software can be selectively applied to any single camera, group of cameras, or system wide via integration with a video management system (VMS). This allows users to leverage their existing investment in video systems, transforming these systems from reactive to proactive solutions. While many AI-powered solutions can have hefty hardware requirements, lightweight options with modest hardware needs do exist (for example, ASTRA offered by Active Intelligence). Choosing an option that does not require expensive high-performance hardware can ease the cost justification process.
Implementation of these solutions is often extremely simple. Once installed, the anomaly detection solution spends a period of time monitoring the selected video feeds, using artificial intelligence (AI) and machine learning to understand normal activity in a given area
Once the learning period completes, the anomaly detection software notifies operators in real-time when an abnormal activity is recognized. This allows security personnel and other first responders to take action to remediate the situation, if necessary. The proactive nature of the solution can help prevent potentially dangerous events from escalating, and/or help alert personnel if an individual needs assistance.
Since anomaly detection software does not require rules to be pre-configured, it has virtually unlimited applications for physical security, health and occupational safety, and business intelligence. Anomaly detection software can automatically call attention to a virtually unlimited number of event types. For example, irregular movements of people and vehicles; medical emergencies; suspicious behavior; vandalism and destruction of property; pooling water and flooding; dangerous vehicle movements; slip and fall incidents; theft and home invasion; workplace accidents; crowd gathering and dispersion; unscheduled visitors and trespassing; fire and smoke; and aggressive behavior and fighting… basically, anything outside of normal activity will be detected.
Here is a perfect scenario of an abnormal event that conventional video analytics simply would not notice. Employees are returning to the workplace, but often on flex hours or hybrid schedules. Some employees enjoy working at odd hours or on the weekends when offices are generally not occupied. An employee takes this opportunity to “borrow” some office equipment, removing it from the facility.
Anomaly detection software would automatically report this unusual event, as it would individuals quickly dispersing in a common area or vandals trashing a retail space. Any action outside of “normal” activity for this specific area under surveillance in a specific environment would trigger a notification in real-time. Anomaly detection also never stops learning and will continue to consider new “normal” events and behaviors over time, including season changes, traffic flow, weather, schedule changes, and more.
Anomaly detection software is also completely unbiased – it does not profile or store personal identifiable information that could pose liability issues for companies. All anomalies are identified based on statistical data captured by the software without any profiling or human judgement. This means anomaly detection is ideal for use in nearly any public or private environment.
Anomaly detection technology sets a new standard for preemptive video technology that can be applied to myriad physical security and business intelligence applications across organizations of virtually any size. What’s more, anomaly detection is easy to cost-justify given the vast numbers of ways it can mitigate risks and liabilities.
It is fast and easy to implement using existing video security systems, does not require additional training, significantly reduces the need for live operator monitoring, boosts security and safety, and reduces risks and liabilities. Anomaly detection software is the solution our industry has been waiting for; allowing businesses to better protect their facility and get closer to prevention.