
As number of people traveling continues to rise, airport security become more extensive and complex while facing unique challenges.
- By David Lenot
- Jan 16, 2015

The Prime Minister is lobbying President Obama this week.
- By Matt Holden
- Jan 16, 2015

Middle school students asked to bring canned goods to school, but it's not for a food drive.
- By Ginger Hill
- Jan 15, 2015
New website includes different areas with customized content for dealers, system users and consultants.
A UL-certified central station is now achievable for all.
Central Station Alarm Association’s certification re-enforces Protection 1’s commitment to providing the highest level of service to its customers.
Initiative generates more involvement and funding for U.S. children in need.

Unknown suspects tried to probe the base for security weaknesses.
- By Matt Holden
- Jan 15, 2015

Ways in which Obama proposes America fights against cyber threats with commentary from Yubico CEO.
- By Ginger Hill
- Jan 14, 2015
AQE Series of PoE injectors and extractors bring data and power together.
Increases security for schools and businesses during crisis lockdowns.
Company's first surveillance camera built on advanced 4K ULTRA HD engine for improved business intelligence.
ALLIE made Reuters’ Best of CES list, received the Consumer Electronics Associations Mark of Excellence award, and was honored in both the Digital Imaging and SmartHome sections of the CES Innovations Awards showcase.

Officials have launched an investigation into the attack
- By Matt Holden
- Jan 14, 2015
No penetration of bullet-proof guard booth in November 28 downtown Austin, Texas shooting.
Innovative inter-city security solution for Minneapolis-St. Paul area highlights the power of partnering.
World's oldest programs for design excellence worldwide that receives several thousand submissions from 48 countries across the globe.
Helps to shape physical access control smart card technology in concert with other committee and Smart Card Alliance representatives.

Online discussions regarding the killing of soldiers and police lead to security services entering a state of high alert.
- By Matt Holden
- Jan 13, 2015

Inspire Magazine, an Al-Qaeda publication, publishes article on how to make homemade bombs from household products.
- By Ginger Hill
- Jan 13, 2015
Lyric line features awareness cameras, motion and smoke and intruder detectors that integrate with other home automation products, such as the smart thermostat.
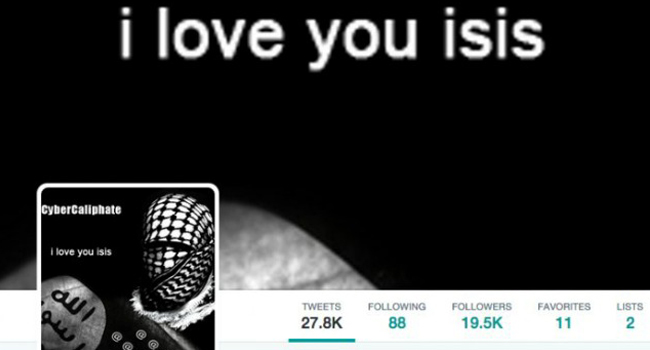
Revealing Tweets from known terrorist group should not be taken lightly.
- By Ginger Hill
- Jan 12, 2015

From one of the black boxes being retrieved from the AsiaAir flight crash to talks of speeding up nuclear talks, this is top news you need to know.
- By Ginger Hill
- Jan 12, 2015

France is taking a number of measures in a reaction to last week’s terrorist attacks.
- By Matt Holden
- Jan 12, 2015
Retired Special Forces Officer to present: “Leadership Is A 24/7 Job.”
Synectics to explain and demonstrate how achieving protection of crucial assets for economic and social development is as much about people as it is about technology at Intersec 2015 in Dubai.
Ideal for any facility that requires detailed surveillance with IP and analog cameras, high image quality and zoom capabilities.

Armed boats and police dogs are just a couple of the ways officials are protecting the trial.
- By Matt Holden
- Jan 09, 2015
iTRUST 2.0 POE+ powered, server-less, IP access control product launches and promoted in Metro New York, New Jersey and the New England area.

From his hotel room in Moscow, Edward Snowden has a thing or two to say about digital attacks. (Video included).
- By Ginger Hill
- Jan 09, 2015