
Even if an organization decides to pay a ransom against the FBI’s advice, they should report the crime to law enforcement, according to the FBI alert.
- By Haley Samsel
- Oct 07, 2019

In the latest ransomware attack scourge, three hospitals in Alabama were able to continue serving existing patients but said they could not take new cases.
- By Haley Samsel
- Oct 04, 2019

The French government plans to introduce a program called Alicem that will require residents to take a selfie video to compare to their passport photo.
- By Haley Samsel
- Oct 04, 2019

Security researchers found 11 significant vulnerabilities in devices that use the IPnet software, though there are no confirmed incidents involving takeovers of the devices.
- By Haley Samsel
- Oct 03, 2019

The Department of Homeland Security is refocusing its efforts on cyber threats to aircraft, and the Air Force is sponsoring “hacking villages” to discover hacking vulnerabilities.
- By Haley Samsel
- Oct 02, 2019

Two of the biggest trends today, particularly in the security surveillance and IoT realms, are border security and the emergence of local governments transforming their communities into smart cities.
- By Kevin Taylor
- Oct 01, 2019
Contractors will face big changes and tight timelines next year when the Defense Department institutes its new Cyber Maturity Model Certification framework
- By Derek B. Johnson
- Oct 01, 2019

Under GDPR, companies can be fined for not having their records in order, not notifying the supervising authority and those affected by a breach, or not conducting an impact assessment.
- By Richard Kanadjian
- Oct 01, 2019
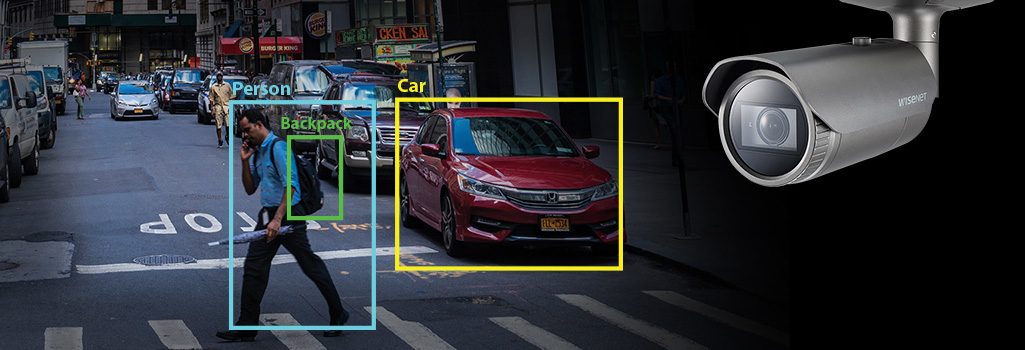
Today, there are in-depth discussions about what ‘might be’ possible with AI, machine and deep learning-based analytics products on the market.

4.9 million users have been affected by the data breach, which DoorDash discovered in the past month.
- By Haley Samsel
- Sep 30, 2019

The chamber also approved funding for the Department of Homeland Security’s cyber arm, with $1 billion dedicated solely to cybersecurity.
- By Haley Samsel
- Sep 27, 2019

The bill is part of an ongoing saga between China-based Huawei and the federal government, which believes Huawei is collaborating with Chinese spying efforts.
- By Haley Samsel
- Sep 26, 2019

The new system may advance the country’s widespread use of surveillance technology in public spaces.
- By Haley Samsel
- Sep 25, 2019

Jarrett William Smith gave detailed instructions about how to build an explosive device to an undercover FBI agent, according to a criminal complaint filed Monday.
- By Haley Samsel
- Sep 24, 2019

The company originally planned to phase out security patches for Windows 7 in January. Now, Microsoft will continue issuing free updates for election systems around the world.
- By Haley Samsel
- Sep 24, 2019

The fight over increased funding for election security is far from over, though: The House and Senate still need to agree on a number for the final version of the bill.
- By Haley Samsel
- Sep 23, 2019

The issue gained renewed attention after a mass shooter used Facebook to live stream his murder of over 50 people at a mosque in Christchurch, New Zealand.
- By Haley Samsel
- Sep 20, 2019
The state said it would redevelop its vote tallying system so that voting machines no longer print receipts with QR codes, which Secretary of State Jena Griswold says could be hacked.
- By Haley Samsel
- Sep 18, 2019

A new investigation discovered that the medical images and health data of more than 5 million patients in the U.S. was readily accessible on the web without a password or login.
- By Haley Samsel
- Sep 18, 2019

Hackers are targeting IT service providers as a means of attacking dozens of organizations at once and potentially reaping bigger financial rewards.
- By Haley Samsel
- Sep 17, 2019