
Officials have launched an investigation into the attack
- By Matt Holden
- Jan 14, 2015
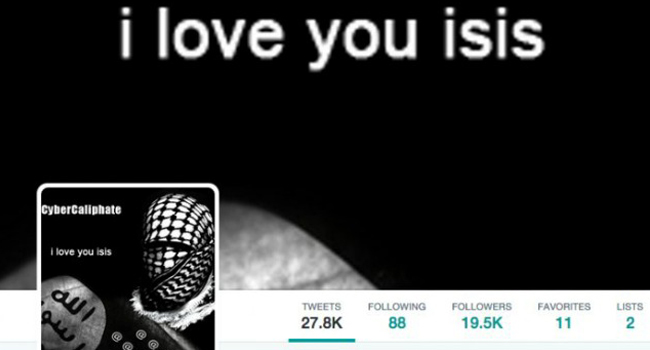
Revealing Tweets from known terrorist group should not be taken lightly.
- By Ginger Hill
- Jan 12, 2015

From his hotel room in Moscow, Edward Snowden has a thing or two to say about digital attacks. (Video included).
- By Ginger Hill
- Jan 09, 2015
Credential provides additional validation of TSC Advantage’s holistic approach to cyber risk assessment.

North Korea’s internet was down for several hours before being restored Tuesday.
- By Matt Holden
- Dec 23, 2014
The BlackBerry Enterprise Server (BES 12) will be integrated into the phone.
- By Matt Holden
- Dec 22, 2014
"The Interview" will not be seen in theaters or on pay-per-view or on any other platform.
- By Ginger Hill
- Dec 18, 2014

The deputy director of the center is willing to look beyond his borders for cutting edge techniques
- By Matt Holden
- Dec 17, 2014
Solution designed as a cost-effective, high-storage efficiency appliance that secures vital company digital assets and deploys business-critical applications.

Advocacy group claims program is unconstitutional because it violates the 4th Amendment.
- By Ginger Hill
- Dec 17, 2014

These tips will help secure pay data when shopping online
- By Matt Holden
- Dec 16, 2014
Provide comprehensive cybersecurity information assurance, engineering and logistic support for Remote Visual Assessment (RVA) video surveillance system.
True self-replicating parasitic virus, VirRansom, demands 0.619 Bitcoin to let you back into your PC.

Government agency attempts to stand its ground against political leader.
- By Ginger Hill
- Dec 05, 2014

Social Security numbers appeared more than 1.1 million times in 601 publicly-posted files stolen by hackers.
- By Matt Holden
- Dec 05, 2014
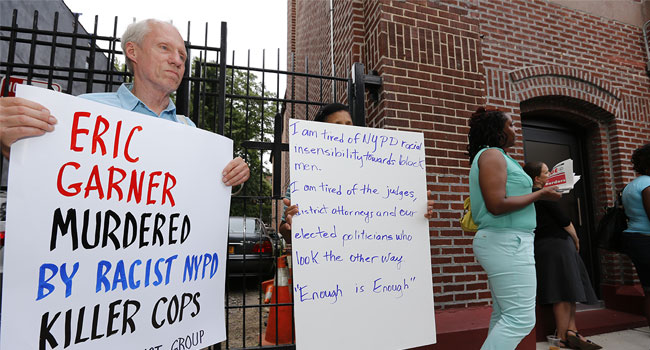
Critics attack NYPD after on social media after "wehearyou Tweet comes out soon after Eric Garner decision.
- By Ginger Hill
- Dec 04, 2014

A new report indicates consumers remain concerned about medical technology and the security of their health information and data.
- By Matt Holden
- Dec 04, 2014
Watch out for cybercriminals looking to make some extra cash during scam season - its a social engineering bonanza with threats on multiple fronts.

Business operations are coming back online after crippling attack.
- By Matt Holden
- Dec 02, 2014

FBI gains fresh intelligence and issues a security bulletin last night.
- By Ginger Hill
- Dec 01, 2014