
No matter how good an organization’s perimeter defenses and threat detection systems are, it really is just a matter of when it will get breached.
- By Tom Hickman
- Jun 06, 2019

The AMCA said they hired a third-party external forensics firm to investigate the Quest Diagnostics data breach
- By Kaitlyn DeHaven
- Jun 05, 2019

Quest Diagnostics has warned its 12 million customers that their personal, financial and medical data may have been exposed.
- By Sydny Shepard
- Jun 04, 2019

The endlessly growing mountains of personal, private data collected as part of routine transactions in our digital world continue to be a target for cybercriminals, who are moving beyond digital theft to the real world by targeting the servers that contain this data.

First American Financial Corporation was made aware of a flaw that exposed their client's mortgage documents.
- By Sydny Shepard
- May 29, 2019

Baltimore has been inching closer to restoring computer systems after a ransomeware attack on May 7.
- By Sydny Shepard
- May 24, 2019

While companies and individuals embrace innovation, cybercriminals make use of the new backdoors to improve the scope of their hacking.

Security is now being analyzed during the development process to account for every variable.
- By Jeff Keyes
- May 20, 2019
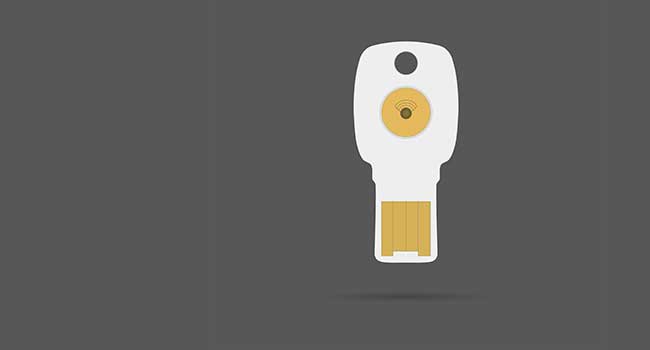
Google announced its Bluetooth security keys could be vulnerable to attack.
- By Sydny Shepard
- May 17, 2019

Here's what you need to know about WhatsApp's major security flaw.
- By Sydny Shepard
- May 16, 2019

A bug in the iOS Twitter app impacted the privacy of its users.
- By Sydny Shepard
- May 15, 2019

Binance is making significant security changes after 7,000 Bitcoins were stolen.
- By Sydny Shepard
- May 13, 2019

Ever, a photo storage and backup app, reportedly trained a commercial facial recognition system using millions of images uploaded to the service without notifying users.
- By Jessica Davis
- May 10, 2019

Technology is providing small and medium-sized businesses (SMBs) of all industries a tremendous opportunity to grow and better manage their business.
- By Manny Johl
- May 09, 2019

The tenth version of Android will include finer control over privacy and improvements to Android security updates, Google announced Tuesday at its I/O 2019 event
- By Jessica Davis
- May 08, 2019

Find out how you should respond to being hacked.
- By Jerry Young
- May 06, 2019

The U.K. government is looking to step up IoT security against cybercriminals.
- By Sydny Shepard
- May 02, 2019

There are a number of common misconceptions about endpoint security.
- By Jerry Young
- Apr 29, 2019

Six reasons companies should implement a Zero Trust Security Mode.
- By Michael Sciacero
- Apr 26, 2019

Some common areas and issues to keep growing your business, not your security risk.
- By Gary Brown
- Apr 26, 2019