
New video shows Michael Brown at the convenience store police say he robbed hours before he died.

Intruder breaches White House grounds and was arrested near residence entrance.

Several people were injured by a man with an axe on Thursday night in Germany.
Hanwha Techwin America is introducing their advanced web site.
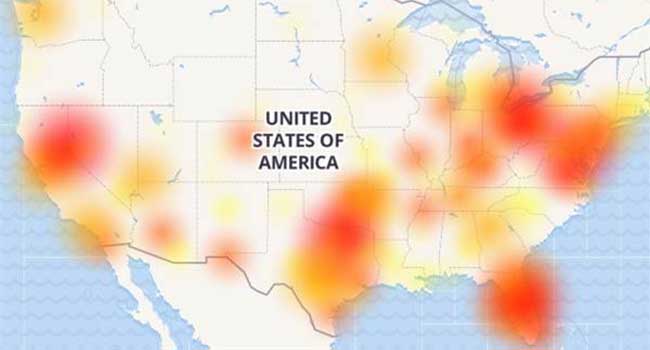
Users of AT&T’s wireless network found themselves without the ability to call 911 last night.

Today as the cybersecurity landscape continues to evolve at breakneck speed, so do the threats, and the amount of data we have sitting with the different organizations we deal with is growing each day.
- By Brett Hansen
- Mar 09, 2017

WikiLeaks released thousands of documents that it said described hacking methods of the CIA.

Jewish Community Centers around the U.S. faced another wave of bomb threats on Tuesday.

UK’s Senior Counter-terrorism police officer said UK security services have stopped 13 terror attacks since 2013.
Maisano brings over 15 years of channel expertise, delivering record-setting sales and revenue growth in competitive markets for companies like Acronis, Ingram Micro and Seagate Technology.
Westinghouse Security Adds Starlight Color Camera Series to Lineup
Leading Colorado-based access control manufacturer brings new features to its Pure Access Software to better serve customers
Bosch takes further steps in cooperation with Sony towards setting new standards in the field of video security solutions

Over the weekend, President Trump publicly accused former-president Obama of wiretapping the phones in Trump Tower before the election.
Milestone Systems names Bosch its 2016 Camera Partner of the Year

Milestone Systems is the number one VMS worldwide, but they are searching for more.

Most countries have fallen victims to traditional style of cyber attacks originating from other countries.
Security Professionals Run for Children at Mission 500’s 8th Annual Security 5K/2K at ISC West