The pharmaceutical industry is a business exposed to many unique risks. Attaining capital, investing in intensive research and development, the uncertainty of FDA approval and the constant shroud of legislative risks are merely some of the many significant challenges that innovative pharmaceutical companies regularly face.
- By Ralph C. Jensen
- Jan 01, 2017
Effective campus security consists of more than just a budget line-item and the proverbial “knocking on wood” in today’s day and age.
- By Minu Youngkin
- Jan 01, 2017
One of the most important things that you can do at the start of a new year is to refine your business plan with both short and long-term goals.
- By Barbara Holliday
- Jan 01, 2017

Students and the facilities in which they attend classes face more threats in today’s society than at any other point in history.
- By Russell Ost
- Jan 01, 2017
Video surveillance permeates our lives today; it is part of a changing world. We recently sat down with Jeff Whitney, vice president of marketing for megapixel camera manufacturer Arecont Vision to get an industry insider’s view on where the video surveillance market is today, how we got here, where we can expect it go in the near future, and what his own company is doing to keep up.
- By Ralph C. Jensen
- Jan 01, 2017
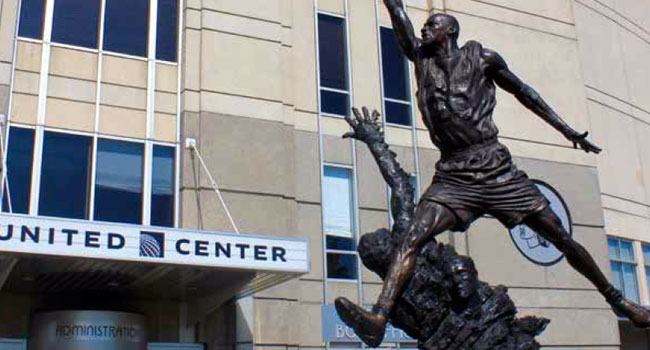
Frustrated with a faulty analog security setup, Chicago’s United Center set out to raise their technology standards and centralize operations through a network system.
- By Mark McCormack
- Jan 01, 2017

Campus security, both in a corporate and higher education setting, can be improved by leveraging data from access control systems to drive future security decisions.
- By Dave Bhattacharjee
- Jan 01, 2017

Pensacola christian college (pcc), in northwest florida, is located just off the warm emerald waters of florida’s gulf coast. pcc became a reality in 1974 when 100 students arrived at the college’s one building.
- By Tracie Thomas
- Jan 01, 2017

In our last contributed article, Anixter examined the topic of “Sourcing to Become a Leaner Organization.” Here we take a look at another important component of increasing profitability—Reducing and Managing Non-Productive Labor.
- By Brad Stevens
- Jan 01, 2017

Maintaining the security of our nation’s water supplies is serious business. Attacks from a lone vandal to a team of foreign terrorists could, within hours, result in widespread illness or economic disruption.
- By Bruce Czerwinski
- Jan 01, 2017

In an ideal world, security personnel would never be faced with making quick decisions in difficult situations. They would not have to respond to incidents or emergencies because such things would not occur.
- By Zebedeo Peña
- Jan 01, 2017

College and university campuses have hundreds— even thousands—of outdoor acres to secure, from parking lots to exercise trails. however, many of the standard security solutions— locks, access control and intrusion alarms—used to protect the indoor environment have little impact outdoors.
- By Bruce Czerwinski
- Jan 01, 2017
Educational institutions face an increasing risk environment. recent high-profile incidents emphasize these risks and magnify the vulnerabilities that educational facilities face. this has led to an increase in public demand for improved security solutions across campuses.
- By Brandon Reich
- Jan 01, 2017
There is an old saying about how everything is bigger in Texas, and in the case of Lexus of Lakeway, the expression certainly rings true.
- By Steve Birkmeier
- Jan 01, 2017
At first blush, the concept of bringing military operational and intelligence know-how to campus security may seem strange.
- By Benjamin Bryant
- Jan 01, 2017

Vehicle attacks, hacks and police ambushes make the list of top physical security events of 2016.

Thanks to a number of new technology advancements, power supplies and transmission solutions with network management features are a natural progression for ensuring the reliability of today’s IP-based physical security systems.
- By Ronnie Pennington
- Dec 29, 2016

Most products like firewalls, anti-spam, and network intrusion devices are designed to keep hackers on the outside from getting in, but that outward approach does not address an equally dangerous situation: the insider threat.
- By Isaac Kohen
- Dec 28, 2016