A website that contains information about children in case they go missing has admitted a glaring security hole that leaves the data of over 1,500 children exposed.
- By Sydny Shepard
- Feb 25, 2016

MasterCard announced new security measures for mobile smartphones and tablets.
- By Sydny Shepard
- Feb 24, 2016

The FBI is asking for Apple’s help to crack the code on an iPhone owned by one of the San Bernardino shooters.
- By Sydny Shepard
- Feb 17, 2016

Security companies are making a splash at the 2016 Consumer Electronics Show, take a peek into our roundup of the coolest products.
- By Sydny Shepard
- Jan 08, 2016

AirportXP, a mobile experience tool, allowed travelers to log their satisfaction with airport security checkpoints.
- By Sydny Shepard
- Dec 22, 2015

Google research team finds 11 security flaws on Android device.
- By Sydny Shepard
- Nov 04, 2015

These technologies are changing the game when it comes to keeping you safe and giving you peace of mind.
- By Sydny Shepard
- Nov 03, 2015

A new study shows how mobile networks around the world have been hacked via bugs in the code.
- By Matt Holden
- Oct 15, 2015

In order to stay relevant in specific markets, many organizations are creating mobile applications and the public safety industry is no exception.
- By Phil Harris
- Oct 07, 2015

After an attack on the App Store, iPhone and iPad users in China and Taiwan are still at risk.
- By Matt Holden
- Oct 05, 2015

A new report from Bluebox Security says the top 10 travel apps in the iOS and Android app stores are all riddled with security flaws. Bluebox says encryption app data, insufficient protection against man-in-the-middle attacks, and leftover administration or debugging code are the biggest issues for the iPhone and Android devices.
- By Matt Holden
- Sep 15, 2015
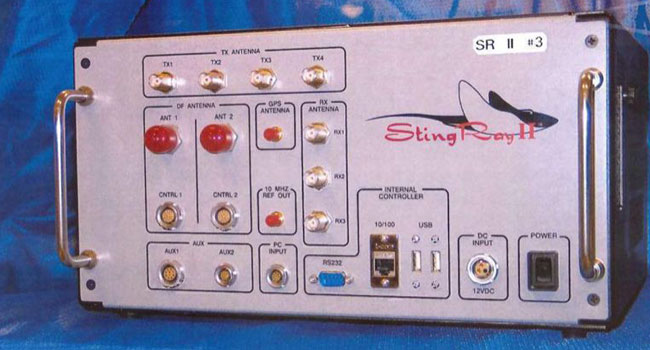
First effort to create uniform legal standards for federal authorities to track cellphones.
- By Ginger Hill
- Sep 14, 2015

You might not realize just how much you're actually sharing with complete strangers.
- By Ginger Hill
- Sep 11, 2015
Companies to work together on all aspects of sales, marketing and manufacturing of Bluetooth readers.

The continuing threat posed by global terrorism has driven huge amounts of government investment into electronic surveillance, as well as both wide and targeted physical monitoring systems in our cities.
- By Matthew Naylor, Nicholas Dynon
- Sep 01, 2015

Internet-connected vehicles becoming target for tech-savvy cyber criminals.
- By Ginger Hill
- Aug 05, 2015
Symmetry CompleteView VMS and Symmetry PowerProtect NVRs offer faster processes, performance gains and increased storage.

The devices can be hacked using a simple MMS message.
- By Matt Holden
- Jul 28, 2015

Smartphone used to record pat-down process and the exchange of unpleasantries.
- By Ginger Hill
- Jul 23, 2015

Since introduction of computer passwords, not much has changed...until now.
- By Ginger Hill
- Jul 13, 2015