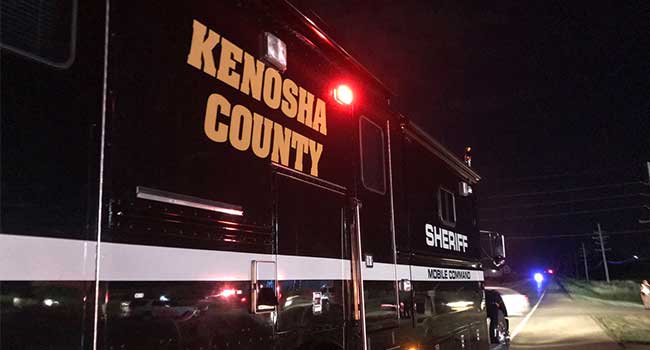
Three men were killed in a shooting at a Wisconsin dragstrip last Sunday night.

Over the weekend protesters and counter protesters clashed in Charlottesville, Virginia, leading to violent clashes and a deadly vehicle attack.

If someone told you that a particular system or product fails to work properly 98% of the time, chances are you would call that system or product an abject failure.
- By Jorge Perdomo
- Aug 14, 2017

Businesses can effectively close the market for ransomware attacks by implementing these three strategies.
- By David Wagner
- Aug 11, 2017
Advanced Mapping Interface and Enhanced Reporting Simplify the User Experience

Fiber optic sensing is a new tool that may address threats
- By Thomas Cohen
- Aug 10, 2017

Security forces in Wales are asking people to take a sip out of their water bottles to prove there is not acid in them.

Police have shot and wounded a man after a dramatic car chase following an attack on soldiers.

UK firms could face up to £17 million in fines if they fail to protect themselves from hackers.
Wisenet P series Delivers Innovation, Performance and Reliability

The Transportation Security Administration released a video on their YouTube channel explaining the layers of security that go into protecting an airport.

The act has since been named an “act of terrorism.”
AMAG Technology welcomes Telaeris to the Symmetry Preferred Partner Program.

The UK, nervous about hackers gaining access to moving vehicles, has added strict guidelines to connected cars.

Fraudsters cast their nets wide in the hopes of snagging unaware and unsuspecting consumers who will unwittingly download malicious applications on to their mobile devices which can then be exploited for short or long-term financial gain by cybercriminals.
- By Michael Lynch
- Aug 07, 2017

The Secret Service will be looking at whether unmanned aerial vehicles could be useful in the protection of the president.
Leading event management security provider offers Free Guide for Oversized ID Card Printers to Event Managers; helps improve security at large-scale events.