
An officer in Little Elm, Texas was killed in a standoff with a gunman.
Here’s a little more detail about SDC’s new hires.
Bridge Safety and Security Bolstered with Key Management System

Houston and Miami saw a violent close to Martian Luther King Jr. Day when gunfire erupted injuring 12 people in all.
Hikvision provided cameras used for instruction and security at Kids World in Utah

4 people were killed in the gunfire and 1 was killed in the stampede as people attempted to leave the nightclub.

Essential questions you must ask a private security company to ensure that you have picked a right team for your property and workplace.
- By Ahmad Hamidi
- Jan 13, 2017
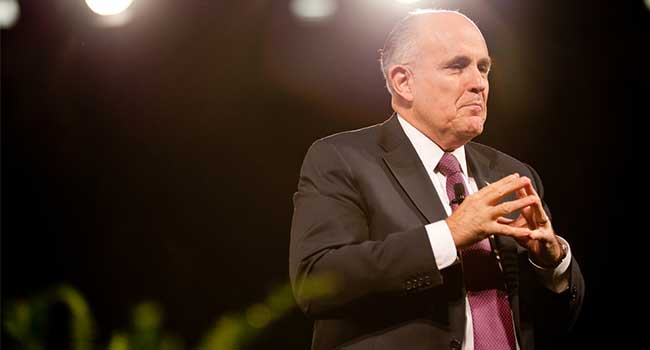
President-Elect chooses Rudy Giuliani to hold private industry meetings on cybersecurity.

Following two shooting incidents that killed one and injured nine more, the city is planning new security measures on Bourbon Street.
Hyperconverged infrastructure technology leader hires two seasoned industry professionals with deep experience in the region.
Bucks County becomes first agency in the State of Pennsylvania to implement ASAP; Alarm users to benefit from faster, more accurate emergency response.
Powerful access and control solution gives customers complete site control

Maybe it’s time for a different (and maybe more affordably efficient) approach.
- By Mike McCamon
- Jan 11, 2017
Vicon Valerus is built on open standards
More than $800K Raised in 2016 for Children and Families in Crisis Across the U.S.

Tuscaloosa police confirm a hostage situation at Alabama Credit Union.
Growth from 2016 carries over to 2017 with the addition of Mike Botten to the LVC sales team.
The addition of Charlie Johnson to the LVC sales team is an exciting one.