 Employed and contracted personnel that have access to sensitive facilities present one of the most significant threats to our nation’s critical infrastructure and public venues. The most basic elements of physical security require that we establish a hardened perimeter and limit access to individuals who are essential to operations and economic vitality. It seems like a simple concept, yet public and private Risk Managers still struggle to implement effective personnel assurance programs for employed and contracted resources that support construction, maintenance and general operations.
Employed and contracted personnel that have access to sensitive facilities present one of the most significant threats to our nation’s critical infrastructure and public venues. The most basic elements of physical security require that we establish a hardened perimeter and limit access to individuals who are essential to operations and economic vitality. It seems like a simple concept, yet public and private Risk Managers still struggle to implement effective personnel assurance programs for employed and contracted resources that support construction, maintenance and general operations.
On June 1, 2015 the Department of Homeland Security’s Inspector General issued a report disclosing covert operations that were 96% successful in sneaking fake explosives and banned weapons through airport security checkpoints throughout America. One week later, another Inspector General report revealed that TSA failed to identify 73 active aviation workers with links to terrorism. These direct security breaches resulted in the exposure of massive, system-wide vulnerabilities that can easily be exploited to execute a large-scale terrorist attack.
How can we effectively mitigate the insider threat? What improvements to perimeter security and personnel assurance are required to ensure that only trusted resources have access to our nation’s transportation centers, utilities, healthcare facilities, academic institutions, and public landmarks?
Establishing and Maintaining Trust
All too often, disconnected, fragmented systems and operations have prevented Risk Managers from accomplishing their goals using disparate HR, vetting, policy administration, training, badging, access control, and incident management systems. Certifiable ‘trust’ can only be achieved through integrated systems that privately share individuals’ critical identity, compliance and performance data. An individual whose personal identity has been validated does not necessarily mean that they belong in a particular location.
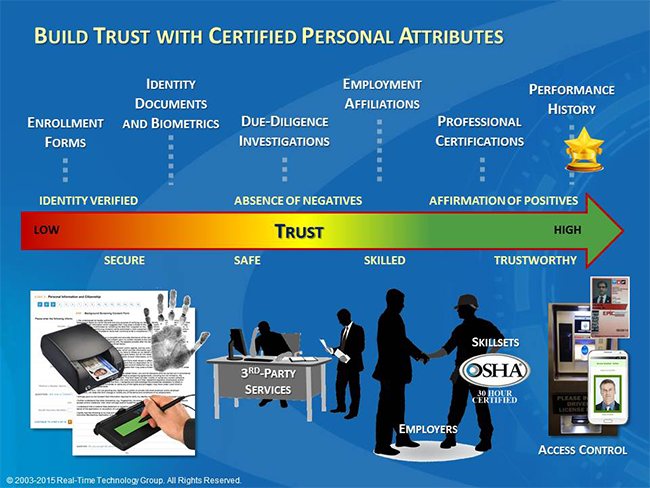
A ‘Trust Value Chain’ (see Figure 1 – Trust Value Chain), as utilized by RTTG’s Real-Time Verification technology, links certified ‘attributes' to known (i.e. positively identified) individuals as they are:
- Vetted and determined to be ‘secure’;
- Trained and considered to be ‘safe’; and
- Deemed ‘trustworthy’ through adherence to Standard Operating Guidelines (SOGs) over time.
Figure 1 – Trust Value Chain
One Size Does Not Fit All Risk Profiles
The collection of various, certified attributes results in comprehensive identity profiles that help assure that all personnel continually comply with the most up-to-date safety and security requirements. Unfortunately, it’s not a one-size-fits-all equation. This critical information may include, but is not limited to: identity data, background, employment affiliations, medical and fitness exams, professional accreditations, safety and other occupational training, public record alerts (including social media), and past performance and incident histories (see Figure 2 below –Certifiable Personal Attributes).
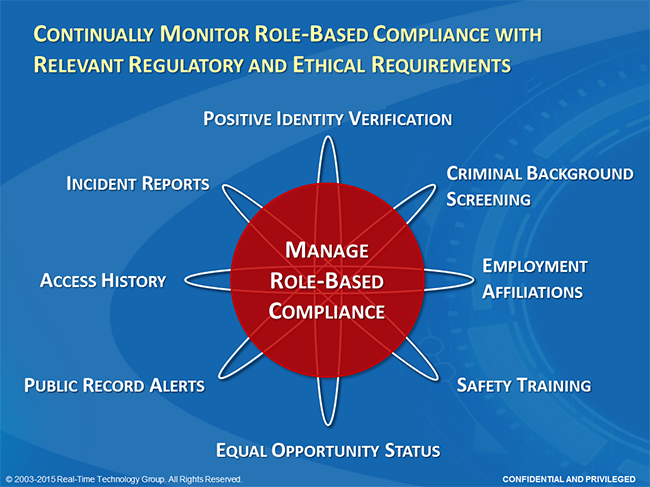
Establishing unique definitions of trust for various roles and risk profiles is a critical first step in the successful deployment of Trusted-Resource Management Systems. Specific, relevant criteria for on-going evaluation must be aligned with duty requirements of diverse job responsibilities and associated access rights.
This consideration of relevancy is critical in meeting the regulatory and ethical demands of personal privacy protection. Failure to consider the relevancy of various due-diligence and vetting initiatives can leave an organization exposed to right-to-work legal action. On the other hand, failure to address common-knowledge vulnerabilities, such as fraudulent employees or contractors, may result in accusations of negligence. The ability to dynamically specify access requirements at a particular secured location, and actively measure individuals’ compliance with the defined criteria, delivers a purely efficient and effective method for finding a fair and defensible balance between security and privacy.
Operational Quality Depends on Affordable Trust
How can we trust that compiled identity profiles accurately represent the integrity, compliance, and on-going performance of an individual? In order to ‘certify’ these critical data elements, we must create trustworthy processes for the assignment of authentic attributes to individuals’ profiles. State-of-the-art Trusted-Resource Management Systems enable Risk Managers to authorize independent, 3rd-party Service Providers of specific attributes (e.g. vetting, screening, fitness evaluations) as legitimate ‘Issuing Authorities’, thereby strictly limiting the assignability of unique certified attributes. This flexible methodology allows local Risk Managers to dynamically control access requirements, instantly reacting to credible threats, and optimally controlling resource expenditures to meet budgetary requirements.
Substantial operational cost reductions can be gained by securely sharing common attributes among regional stakeholders. Advanced Trusted-Resource Management Systems like Real-Time Verification enable otherwise disconnected Risk Managers to share the expense and operational benefits among many facilities, lowering the per-capita cost of personnel assurance programs. The NY-based Secure Worker Access Consortium (‘SWAC’) exemplifies the benefits of sharing critical identity and certification data among regional Authorities. A cooperative effort of Transportation Authorities, Labor Unions, and Contractors; SWAC streamlines and assures the quality of the enrollment, background screening, employment tracking, and public record monitoring of the entire community (over 30k active individuals). The common acceptance of certified personal attributes at all participating facilities eliminates substantial duplication of effort throughout the region.
Finding Needles in Haystacks
Most often, traditional compliance solutions have limited operational visibility and effectiveness. Data collected in back-office silos may be confirmed upon issuance of access credentials, but rapidly becomes obsolete as required certifications expire or become obsolete. Further, on-going behavior of an individual is rarely considered after prerequisite vetting or training is completed. Optimally, this perishable data must be continuously refreshed and validated to assure on-going compliance with relevant safety and security requirements.
New technologies are emerging that help overcome these challenges. Active monitoring of public records now provides continuous validation that individuals effectively maintain their threat-free status after initial background screening is completed. Real-time video feeds from camera systems enable facial recognition technologies that continually search for known offenders, wanted individuals, and persons-of-interest identified by intelligence officers. These innovative features extract optimal value from Trusted Communities like SWAC. Data analytics and exception reports help regional Risk Managers find the ‘needles’ rather than spend their time searching the entire haystack.