
Guns will not be allowed into the Republican convention in July despite the ideals of those attending.
- By Sydny Shepard
- Mar 30, 2016
Vanderbilt has made a number of hires for its global executive leadership team

While banks have been in compliance with the new standardized EMV chip in debit and credit cards, retailers and consumers just don’t care.
- By Sydny Shepard
- Mar 29, 2016

A hijacker attempted to take control of an EgyptAir plane on its way to Cairo.
- By Sydny Shepard
- Mar 29, 2016
Delivers new offerings to help dealers achieve growth.
While ISC West doesn't step into high gear until next Wednesday, April 6 with the opening of the exhibit hall, the actual conference starts the day before with a number of interesting and unique educational sessions.
- By Brent Dirks
- Mar 29, 2016

A shooting occurred in the Capitol Visitor Center March 28.
- By Sydny Shepard
- Mar 28, 2016
ISC West is almost here; check out the most talked about booths on the show floor.
- By Sydny Shepard
- Mar 28, 2016
I’ll be heading to my first ISC West, so I thought I’d clue you in on all the things I’ve been told to prepare for at ISC West 2016.
- By Sydny Shepard
- Mar 28, 2016
Bridges IT Security and Physical Security in support of IoT
Paxton has appointed Dale Clement as Regional Sales Manager for the Western US and Paul deLaski for the Northeast US.
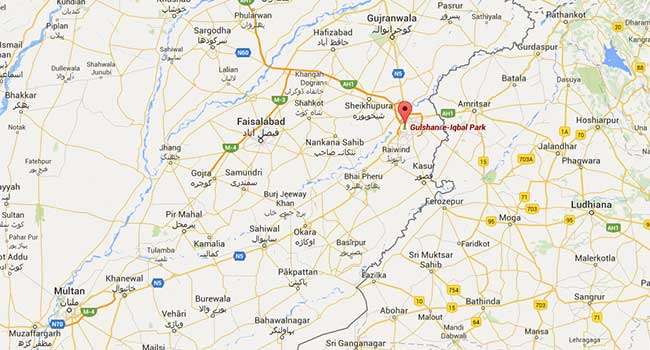
Without warning, a bomb explosion ripped through a park where Pakistani Christians were celebrating Easter, killing 60 and wounding about 400.
- By Sydny Shepard
- Mar 28, 2016

In late March, a flight attendant was trying to board a plan with 70 pounds of cocaine. When she was stopped at a security checkpoint to be randomly screened, she took off running.
- By Sydny Shepard
- Mar 28, 2016
With less than a week to go before ISC West officially kicks off, preparing for the tradeshow is a must. This will be my first year attending, and I've often heard stories from other editors about how large this show is. Simply put, it can be very intimidating, especially for those who are either new to the industry or haven't been to many tradeshows of this caliber before.
- By Lindsay Page
- Mar 28, 2016
You already know there are great things in store at this year's ISC West in Las Vegas. Press releases are flying out of corporate offices announcing new and tuned up security solutions. I'm going to mention a few to whet your appetite for the tradeshow.
- By Ralph C. Jensen
- Mar 28, 2016
It's no secret that ISC West has the best of the best in the security industry there to show their latest and greatest. We'll see new products, new solutions, and new companies.
- By Lindsay Page
- Mar 28, 2016

Wrigley field will be opening two and a half hours early on Opening Day to allow fans to acclimate to the new security procedures.
- By Sydny Shepard
- Mar 25, 2016