Fraud prevention, it’s time to get better acquainted with your security team. You may see them in the hallways, have a coffee with them in the breakroom, and possibly join them on the dance floor at your annual holiday party.
- By Daniel Caggiula
- Feb 01, 2017
I’ve been writing, professionally, for 40 years. The first story that I ever worked on was a triple homicide, and a contract murder that was related. Back then, I didn’t think reporting could get any worse.
- By Ralph C. Jensen
- Feb 01, 2017
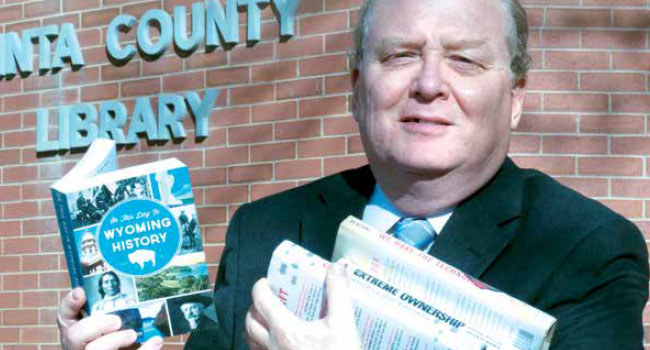
Pick any county in the United States, money is scarce to non-existent, and in the pecking order of who gets the available money, the county library is way down the line.
- By Ralph C. Jensen
- Feb 01, 2017

The abundance of networked solutions and devices—both security and nonsecurity— has exploded in recent years, providing unparalleled convenience and efficiency.
- By Ken LaMarca
- Feb 01, 2017
It can be difficult to decide whether and when to make the transition to new access control technology. Transitions are often delayed over budget concerns or because of worries that the process will adversely impact productivity and workflow.
- By Brandon Arcment
- Feb 01, 2017
Physical identity access management (PIAM) solutions have changed the way leading organizations approach security.
- By Don Campbell
- Feb 01, 2017

Terminal One at JFK International Airport had relied on a limited analog surveillance system and a separate, older IP system that were independent of each other.
- By Courtney Pedersen
- Feb 01, 2017
When it comes to protecting transportation hubs, seaports have their own set of challenges.
- By Anthony Incorvati
- Feb 01, 2017

Earlier in 2016, when Gartner analysts stated that by 2020, 80 percent of all software will be offered on a subscription basis—this did not come as surprise to us at Genetec.
- By Christian Morin
- Feb 01, 2017
Financial institutions have been historically slow to adopt IP video surveillance citing concerns about possibly compromising network security.
- By Stephen Joseph
- Feb 01, 2017
Security threats are on the rise and as IT security teams increase their scrutiny of all network-connected devices, it’s time for some new thinking about the design and maintenance of building security systems.
- By John Szczygiel
- Feb 01, 2017
Based in Milwaukee, Wisconsin, Bell Ambulance Company has been in operation since 1977, growing into the largest provider of ambulance services in the state. The company responds to around 75,000 calls per year and provides a range of services.
- By Fernando Pires
- Feb 01, 2017

In 2015, an ex-deputy shot and killed an unarmed black man.

On Friday, January 27, President Trump signed an executive order that excluded travel from seven countries.

A group of gunman entered a mosque in Quebec and open fired killing six.
Company Leads Change in Customer Interaction with Home Security Providers

Governor Greg Abbot announced the funds would be given to the police department so they could outfit officers with new helmets, bullet proof vests.

Philadelphia is stepping up security as President Trump arrives for the GOP Retreat.

A draft order outlining many things including the revival of torture was published Wednesday.

President Trump is expected to sign two executive orders on Wednesday relating to border security.

A hacker just wants President Trump to change his security settings on Twitter.
IDIS will mark two decades of innovation with customer, partner, and media events and recognitions across the globe in 2017
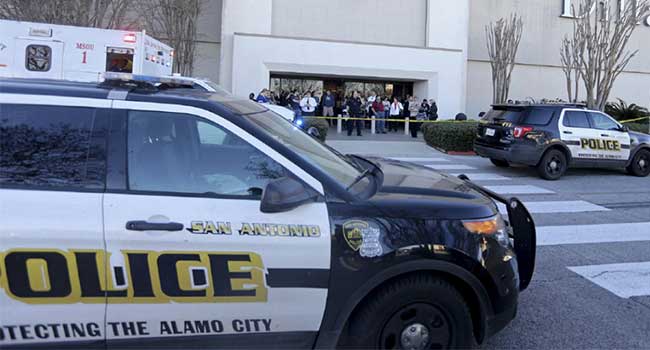
San Antonio police describe the event as a robbery gone, “really wrong.”

Security for the Inauguration is tight as protests swarm and a new president is sworn in.

Washington D.C. Police along with Secret Service and the FBI have been working to secure the Presidential Inauguration for over a year.
Premier provider of integrated Security, Fire, A/V and Electrical and Data Cabling/IT Infrastructures expands executive team & appoints veteran security industry expert to grow company and expand geographical reach
Feenics appointed Paul Cohn as Western Regional Business Development Manager.

A 15-year-old shot a teacher, three students and himself.

An officer in Little Elm, Texas was killed in a standoff with a gunman.
Here’s a little more detail about SDC’s new hires.