Synectics to explain and demonstrate how achieving protection of crucial assets for economic and social development is as much about people as it is about technology at Intersec 2015 in Dubai.
Ideal for any facility that requires detailed surveillance with IP and analog cameras, high image quality and zoom capabilities.

Armed boats and police dogs are just a couple of the ways officials are protecting the trial.
- By Matt Holden
- Jan 09, 2015
iTRUST 2.0 POE+ powered, server-less, IP access control product launches and promoted in Metro New York, New Jersey and the New England area.

From his hotel room in Moscow, Edward Snowden has a thing or two to say about digital attacks. (Video included).
- By Ginger Hill
- Jan 09, 2015

The funny side of video surveillance.

Coach Sumlin of Texas A&M teaches college student the ultimate lesson about respecting the privacy of others.
- By Ginger Hill
- Jan 08, 2015

The gunman also reportedly robbed a gas station in the northern part of the country
- By Matt Holden
- Jan 08, 2015
Hazardous materials monitored through production and transportation.
Secure, wireless, battery-operated, electronic lock that works with company's software for easy management of networked access control.
Focus is on video surveillance with state-of-the-art technology and exceptional technical support.
Company provides IP, wireless and battery-powered access control solutions, providing electronic security for any site requirement.
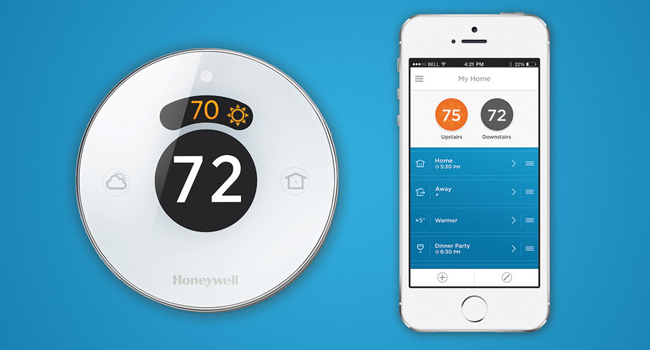
New way for families to stay in control of their home comfort and security while at home or away.
- By Ralph C. Jensen
- Jan 07, 2015
Credential provides additional validation of TSC Advantage’s holistic approach to cyber risk assessment.
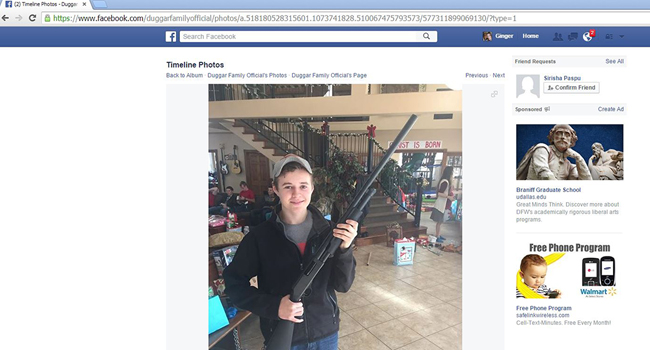
Jedidiah Duggar from TLC's hit show, "19 Kids and Counting," smiles whole posing with shotgun.
- By Ginger Hill
- Jan 07, 2015

Charlie Hebdo, a satirical newspaper, was the target of what many are calling a terrorist attack
- By Matt Holden
- Jan 07, 2015

Offer HD video to clients for approximately the same cost as typical analog gear, with superior results.
- By Jake Blake
- Jan 06, 2015
Google Maps to deliver accurate global geolocation tracking for Absolute Computrace.