
Microsoft plans to invest in new security plan after several high-profile cyber attacks.
- By Sydny Shepard
- Nov 18, 2015

Avast researchers have found a number of vulnerabilities in Smart TVs.
- By Sydny Shepard
- Nov 13, 2015
Fast-growing cyber security software firm attracts new clients in UK and US.

Despite the growing cyber attacks, the health care industry continues to shortchange Americans when it comes to data security.
- By Sydny Shepard
- Nov 12, 2015

Federal authorities say three people have been charged in the largest theft of consumer data from a U.S. financial institution in history.
- By Sydny Shepard
- Nov 11, 2015

Dropbox creates Enterprise version of app to combat their reputation of being a low security file-sharing platform.
- By Sydny Shepard
- Nov 06, 2015

Google research team finds 11 security flaws on Android device.
- By Sydny Shepard
- Nov 04, 2015

In the minutes, hours and days that follow a widespread, widely publicized data breach, most companies scramble to increase their security measures in an effort to overcompensate for their lack of proactive preparation.
- By Denny Heaberlin
- Nov 01, 2015

Poor security habits from employees could lead to a cybersecurity breach.
- By Sydny Shepard
- Oct 29, 2015
SureView Systems partners with integration firm to create easy-to-use platform for customers.
- By Sydny Shepard
- Oct 28, 2015

Cisco's acquisition of Lancope predicted to boost Cisco’s cybersecurity threat defense capabilities.
- By Sydny Shepard
- Oct 28, 2015

Some of technologies leading revolutionaries disregard the Cyber Security Bill as a legitimate solution to the data breaches seen in recent news.

There are many concerns when transferring to the cloud and security is one of the biggest, followed closely by concerns about complying with regulations and losing control of data according to a recent study by 451 Research.

A new study shows how mobile networks around the world have been hacked via bugs in the code.
- By Matt Holden
- Oct 15, 2015

Physical security solutions encompass data-driven knowledge to help anticipate future incidents.
- By Brian McIlravey
- Oct 05, 2015

After an attack on the App Store, iPhone and iPad users in China and Taiwan are still at risk.
- By Matt Holden
- Oct 05, 2015

Success found by taking ideas that seemed like sound concepts and putt them into practice in a scalable way.

A new report from Bluebox Security says the top 10 travel apps in the iOS and Android app stores are all riddled with security flaws. Bluebox says encryption app data, insufficient protection against man-in-the-middle attacks, and leftover administration or debugging code are the biggest issues for the iPhone and Android devices.
- By Matt Holden
- Sep 15, 2015

Every level of government developing ways to deal with physical security as well as the data their program produce.
- By Scott Cheatham
- Sep 14, 2015
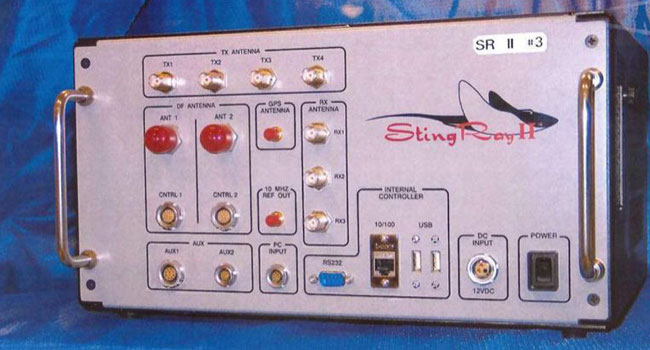
First effort to create uniform legal standards for federal authorities to track cellphones.
- By Ginger Hill
- Sep 14, 2015